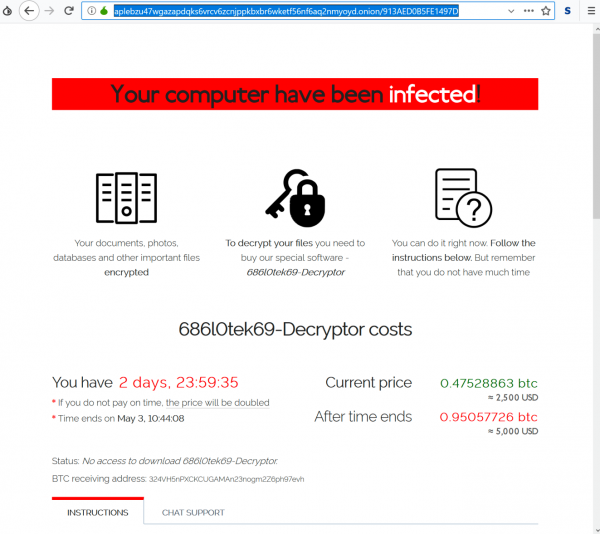
In late April 2019, researchers from Cisco Talos came across a strain of ransomware that raided a web server. The entry point was a remote code execution vulnerability in Oracle WebLogic Server software discovered about a week earlier. The analysts dubbed this infection Sodinokibi. Back then, it seemed that the predatory program was just another ransom Trojan resembling hundreds of others. However, Sodinokibi operators proved this impression wrong a few months later.

As of December, this ransomware lineage is dominating the extortion landscape. It has made dozens of high-profile victims, including healthcare facilities and local governments. Furthermore, its distributors’ toolkit has expanded way beyond leveraging unpatched software flaws to gain a foothold in computer networks. The ransoms raked in by the crooks reportedly reach hundreds of thousands of dollars per compromised organization. What is it that has allowed this campaign to soar in only half a year’s time? Let’s try and figure out.
Dissecting the Sodinokibi business model
Also known as REvil, Sodinokibi ransomware is backed by an underground affiliate program with quality at its core. While the Ransomware-as-a-Service (RaaS) model is nothing new, in this case, it’s an ecosystem with select players that have gained a reputation on the Dark Web.
The campaign got the first major boost in July when a user who goes by the alias UNKN posted a recruitment announcement on a popular hacking forum. This anonymous individual invited other members of the cybercrime community to join the Sodinokibi distribution network that had a “limited number of seats.” Wannabe ransomware peddlers were required to show evidence of quality in terms of the installations they could provide.
One of the perks mentioned in the ad is that the affiliate share starts with 60% and goes up to 70% after the first three ransom payments. The rest is a “royalty” that goes to the proprietors of the Sodinokibi code. The forum post emphasized that it’s forbidden to do business in the Commonwealth of Independent States (CIS) region, including Ukraine, Russia, Belarus, and Moldova.
This RaaS quickly got a number of endorsements from trusted members of the black hat environment, who claimed to be very satisfied with the cooperation and encouraged like-minded crooks to get on board. UNKN also shared a snapshot of the recent incoming payments, where most victims submitted 0.4 BTC (about $3,000), and one coughed up a whopping 26 BTC (worth nearly $200,000 at the time of this writing). According to follow-up comments in the thread, infecting large computer networks is a priority for Sodinokibi authors. This focus explains such a big ransom paid by one of the victims.
The elite crew of affiliates

Shortly after this enrollment began, the Sodinokibi epidemic ran rampant and reached eyebrow-raising heights. According to McAfee researchers’ findings, this spike is a result of cybercriminal syndicates with a substantial malware distribution background coming on stage.
The analysts identified more than 40 unique affiliate IDs in this campaign, with some of these players operating very similarly to the most successful participants of the GandCrab RaaS. For the record, GandCrab was a highly prolific ransomware family whose decline co-occurred with the Sodinokibi debut last spring. Experts have since spotted numerous ties between the two lineages, which I will highlight in more detail further down.
Obviously, quite a few best-performing GandCrab affiliates appear to have switched to spreading Sodinokibi. These crooks are competent in their nefarious enterprise, and their dodgy portfolio includes a diverse set of infection vectors – from RDP hacks to spear phishing and exploit kits. A particularly effective technique is to compromise MSPs (managed service providers) and thereby access large networks of customers associated with them. This is how the felons perpetrated a massive attack against 22 municipalities in Texas in mid-August, demanding $2.5 million for data recovery. All in all, the team of seasoned cybercriminals distributing Sodinokibi is the mainstay of its top position in today’s ransomware landscape.
Connection with GandCrab
As previously mentioned, there are distinct links between Sodinokibi and GandCrab, a species that was once considered the world’s most serious ransomware menace. The similarity isn’t only about the same threat actors in charge of the propagation and the fact that the former emerged as soon as the latter faded away. Analysts have also unearthed patterns in the code that speak volumes about the same source of both infections.
An obvious trait shared by the two pests is the principle of generating unique URLs for communication with the Command & Control server. The hard-coded values for producing sub-path attributes of these URLs are an exact match.
Furthermore, the beta version of Sodinokibi had a number of debug paths containing clues about its legacy. An example is the “gcfin” (GandCrab Final) project name. Another hint is the “gc6” debug path, which is most likely a reference to GandCrab 6, a version that was probably supposed to become the next iteration of the predecessor but never went live. In addition to this, researchers found that REvil and GandCrab v5.03 had a 40% code overlap.
The main striking difference, though, boils down to the behavior of the ransomware architects. GandCrab operators would often include fun functionality in their code. When malware experts analyzed it, they could stumble upon jokes about themselves with subtle shades of mockery and some smileys here and there.
Contrary to this easygoing attitude, Sodinokibi makers adopt a business-only approach and don’t initiate any interaction with the white hats. At the same time, they appear to have a solid reputation and influence in the ransomware community. These facts suggest that Sodinokibi isn’t run by the same people who were behind GandCrab, although there are evident ties between these malefactors. One of the theories is that the new strain is being operated by former GandCrab coders who chose to continue the dirty business while the original proprietors called it quits.
Recent attacks
In September, a wave of the Sodinokibi plague swept across China via a tricky spam stratagem. The infection arrived with booby-trapped emails pretending to be from the DHL courier company. Camouflaged as notifications about delayed delivery of a package, these messages instructed the recipients to download and fill out the attached document, presumably a customs declaration, so that the shipping process could be successfully completed. However, this file was a ransomware executable in disguise.
The trick is that the attachment had a *.doc.exe extension. Since Windows hides file extensions by default, the embedded object looked like a regular Word document with the right icon. Once opened, though, it instantly launched the ransomware attack on the computer.
Another recent campaign relied on a more intricate tactic. A Sodinokibi affiliate hacked a number of popular WordPress websites and injected rogue JavaScript in their HTML code to display a phony Questions and Answers page on top of the original content. Mimicking real discussion between the site admin and a visitor who has a question related to the site’s materials, this faux page looks trustworthy and may entice the user to scroll down the Q&A section.
In response to the alleged asker’s query, the pseudo admin provides a link to download the document of interest. If clicked out of curiosity, this link leads to a ZIP file containing a JScript item that invokes a series of commands to infect the user’s system with Sodinokibi. This multi-layered hoax is clever a combo of social engineering and obfuscation mechanisms that allow the payload to slip below the radar of antivirus tools.
The bottom line
Sodinokibi, REvil, the new GandCrab – no matter what you call it, it’s the nastiest ransomware on the cyber threat map at this point. Its developers and distributors seem to always have new unexpected tricks up their sleeve, and flawless crypto implementation means that victims have to pay up; otherwise, they lose all their data. What about the countermeasures? A little bit of extra vigilance, especially with dubious-looking emails, plus up-to-date backups of the most important files, make any extortion attempt go down the drain.


