“Abort!” “Abort!” CTRL+ALT+DELETE! That’s the kind of panic that’s likely setting in as you realize something crazy is happening with your computer. We don’t blame you. It’s not only about damage to the hardware or the loss of important files, there’s also the danger of stolen financial information, identity theft, and ransomware that’s becoming a growing trend.
Did you know security firm Kapersky Labs processed 360,000 new malicious files in a day back in 2017? The scary part is that’s just one firm and the numbers are growing daily. Computer viruses have upgraded from nuisance pop-ups to much more dangerous and intricate attacks that have the potential to close down entire operations, causing severe financial damage. While there are a number of protection software’s and solutions for computers and devices available today, there are still new threats emerging daily and many have not yet been discovered.
According to a report released by the FBI, over four thousand ransomware attacks are happening each day. And as of late, the industry has discovered a security flaw that exists in devices manufactured as far back as two decades go. From popular makers ARM, AMD, and Intel, experts agree it’s one of the worst bugs ever seen. Referred to as, “SPECTRE” and “MELTDOWN” these vulnerabilities can expose confidential data within a computer system to hackers.
Here’s a closer look at the problem
With “MELTDOWN,” there is a flaw in place that could allow hackers to get past hardware blocks on a device and into the area where applications are run and where the computer’s core memory is stored. Here, they could gain access to information that the application is storing. Think about banking apps, shopping sites, and simple web pages running applications in the browser – they’re all a potential threat. This is the area of the computer that’s holding on to passwords, communications, and other data that if accessed by criminals, could allow for significant security issues.
With “SPECTRE” the issue is a bit more compounded. While it’s difficult for hackers to manipulate, getting protection from the flaw is also complicated. It works by allowing hackers to trick applications that are not flawed into giving up passwords and other confidential and sensitive information.
Experiencing Issues with Your System? It Could be Compromised
Just because your system is acting slow, weird, or even if you have a blue screen, it doesn’t mean these latest flaws have taken over. There could be a number of reasons for your technology woes. If you fear a virus is the problem, here are some warning signs to be on the lookout for:
- Trouble gaining access to commonly used programs. If you can’t use the start menu, control panel, and your anti-virus software, something more might be happening behind the scenes with your device.
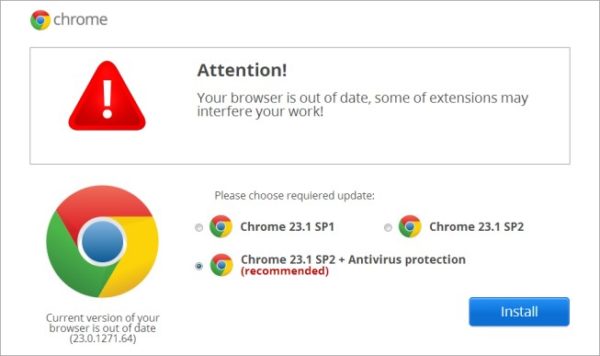
- Mysterious new icons or software. If you open your computer only to notice several newly installed programs and icons that look odd, whatever you do, don’t click them! Run your virus scanning software immediately or take the device to professionals trained in scanning and removing anything potentially harmful that’s made its way on to your computer.
- An exceptionally slow-moving computer, especially if it seems to have started out of the blue. Viruses eat up your system resources, and things such as your RAM, hard drive, and network can all be affected and stop normal functions from responding as efficiently and quickly as they should.
- You’re dealing with constant pop-ups. One of the most commonly used forms is adware where sometimes harmless ads promising free software, invade your computer screen. However, sophisticated attacks using this method may even be able to turn off security software, so proceed with caution.
- Your hard drive has been constantly crashing. If you notice your hard drive is suddenly becoming full or that every time you open an app it crashes on you, it’s time to get serious about security.
- You’re missing files. Another common way viruses can do damage is by removing and deleting files from your computer. It could ruin your operating system, attack it so that it doesn’t work properly, or it could be an attempt to access personal information that may end up being used for identity theft or another crime.
- Strange stuff is happening with your email. Are you noticing emails in your sent folder that you never actually sent yourself? Have friends asking why you sent them an email with a random link? If it wasn’t something you actually sent, you’ve got a virus and it’s spreading.
Now What?
In order to get protection from all of these flaws we’ve mentioned and the danger they can present, you’ll need to have fixes in place even before troubles occur. But, new, emerging vulnerabilities can make achieving this 100% of the time, difficult. If it’s too late and you’ve identified some of the above issues happening on your device, you should contact a team of computer repair professionals to ensure you safely remove the virus for good and still have the option to restore what’s important.
Concerns over MELTDOWN and SPECTRE are also still very real. The issue remains that discovering whether or not an intrusion has taken place is hard. So, the best thing you can do is download necessary patches to update the operating system. Additionally, here are some commonly known best practices to help keep your devices in the clear:
- Use Updated Antivirus Software
- Don’t Click Suspicious Links
- Download Only Trusted Apps
- Use a Firewall
- Perform Regular Backups
Make no mistakes. Computer viruses will remain a critical focus going forward. The best thing you can do if you’re worried about a computer being infected is to get help. Left to continue working on your system, they could do irreparable damage both to your device as well as your financial and personal wellbeing. In today’s increasingly risky, Internet-connected environment it’s more important than ever to remain vigilant about safe computer use and to utilize trusted, up-to-date security solutions to shield yourself from harm.