Introduction
All the while, I have been reviewing data recovery tools for Windows. Today, I’ll be trying out a similar tool for our readers who are Mac users, named Disk Drill. Huge thanks goes out to the team at 508 Software for providing us a Pro license key and other help. As previously, I’ll try my best to be as detailed and lucid as possible. I hope that you’ll like my review as much as I loved writing it.
Getting started
Disk Drill can be downloaded from here. All you need to do is double-click the dmg file to mount it and move the app to your /Applications folder.
If you are a Homebrew-Cask user, it is a one-liner command to install:
brew cask install disk-drill
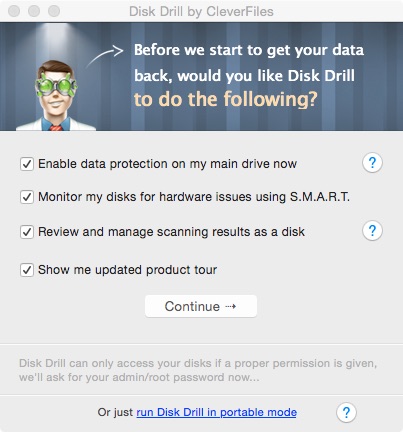
Once it is installed, you start it from the LaunchPad and are greeted with a screen that asks a few questions. After checkmarking what you require, clicking next asks you for your administrator password to proceed.
Once we are past that, the app demonstrates its features with a short tour.
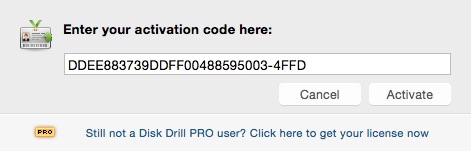
After the tour is over, you are asked if you wish to continue with the free version or upgrade to Pro. I had an upgrade key so I entered it in the field given.
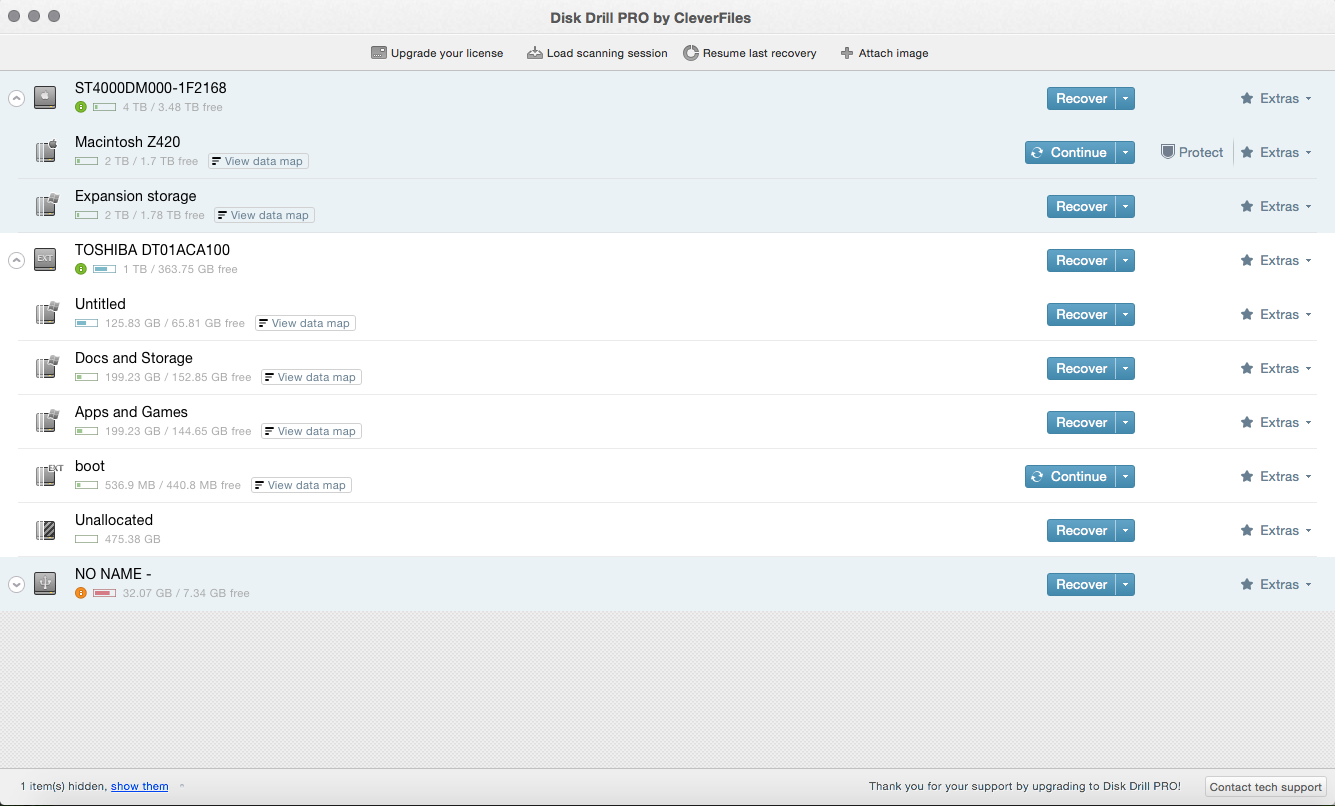
Finally, we are greeted with the start screen.
Usage and experience
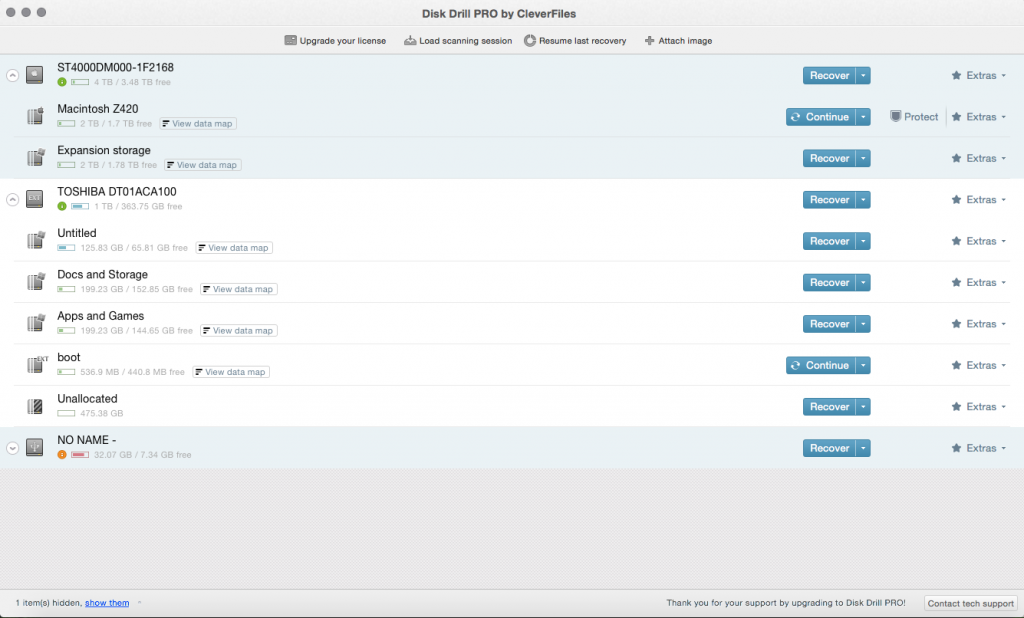
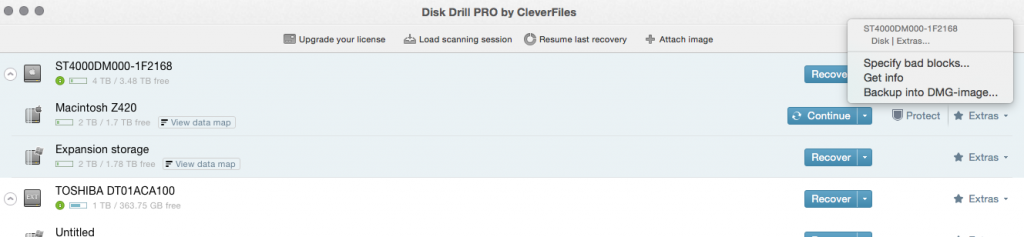
The start screen lists all the hard drives and removable drives connected to the Mac. Clicking the tab on the left side of each entry displays the partitions present on that drive.
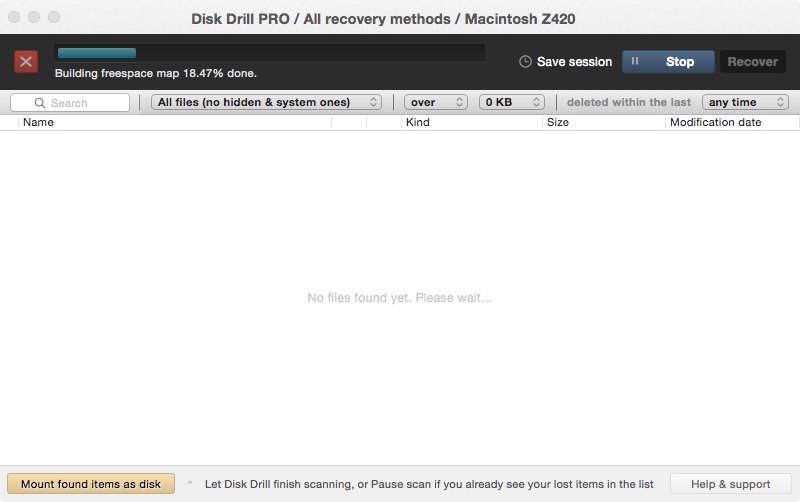
First of all, we’ll start by scanning a drive, the HFS+ drive on which OSX is installed.
The scan takes a while depending on the size of the disk.
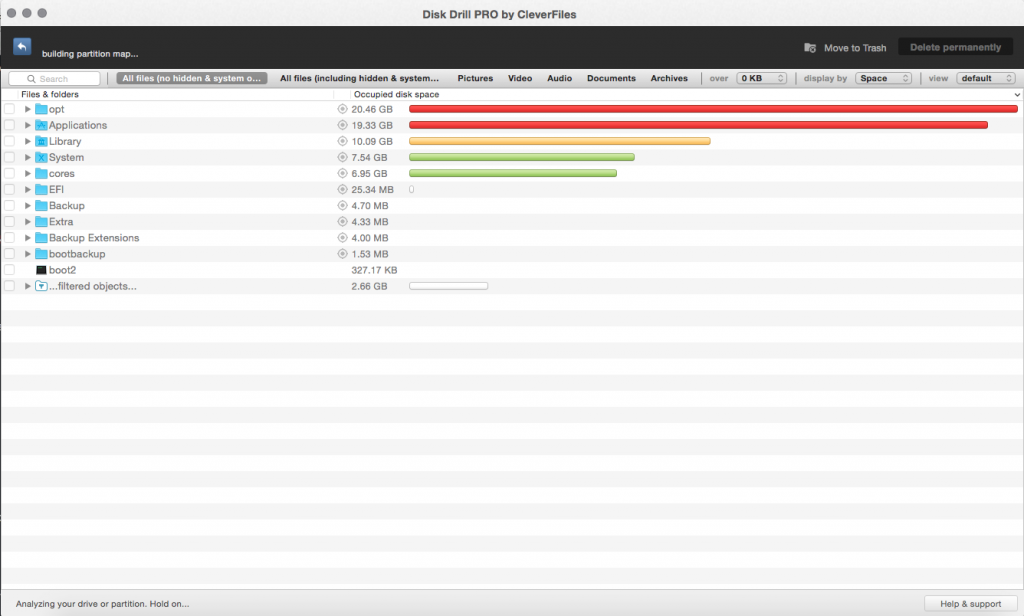
When the disk scan is complete, we see a whole list of files enumerated and reconstructed, the files can be recovered on by one basis or the set of found files can be mounted as a virtual disk.
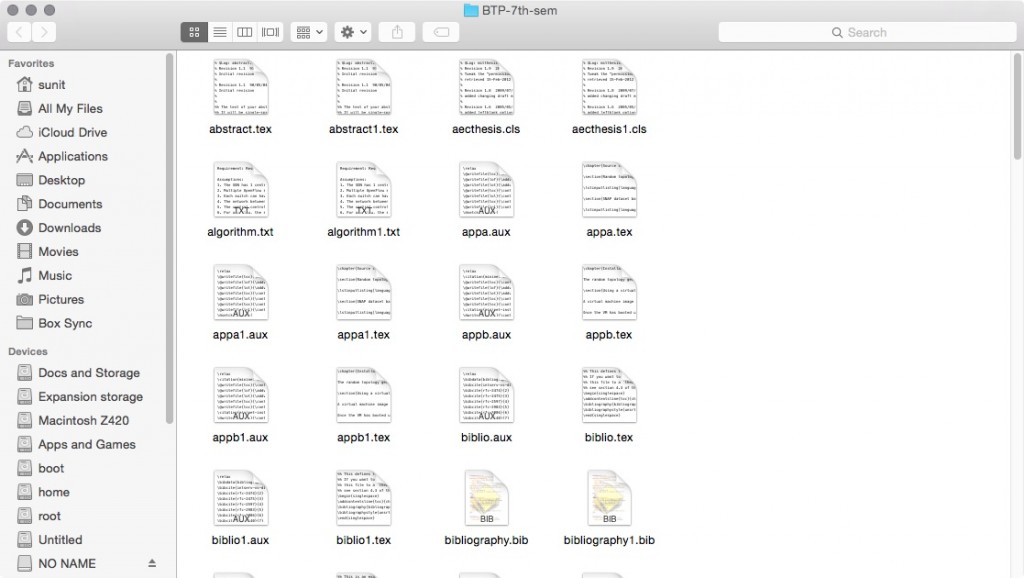
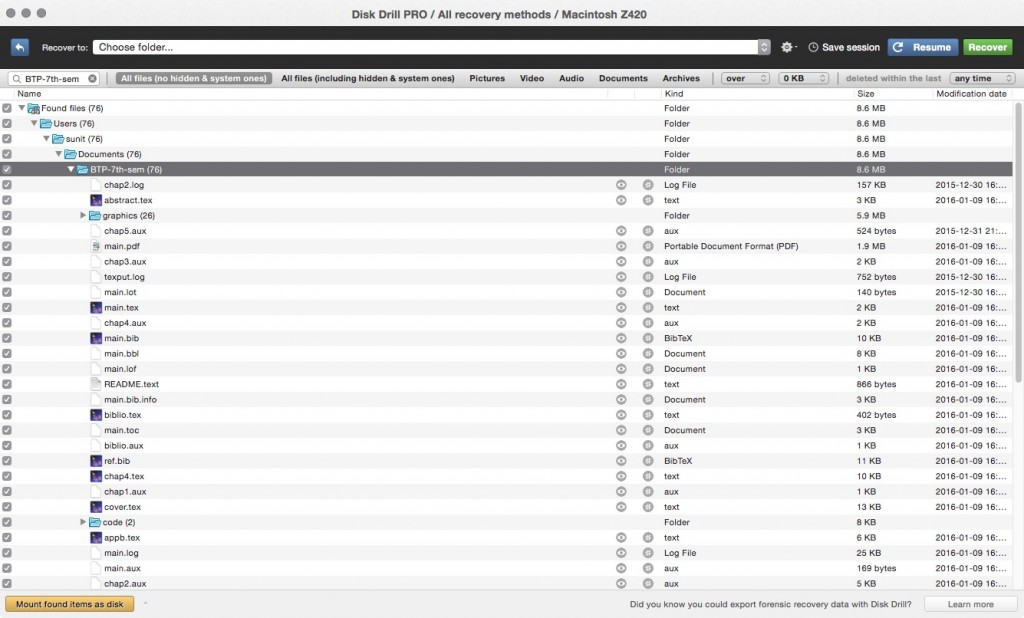
For a random test, I choose a folder.
Here are the contents of the folder.
Also I perform an MD5 checksum of the files in that folder using the Terminal. The results come as follows:
blsz420nandifamilyin:BTP-7th-sem sunit$ find * -type f -exec md5 -r '{}' \;
10288f0a52de797cf30baa6d181cb5af README.bibliography
8a681eb41e84b72cd311b389cc05220f README.main
8063de1459364ee3d044b027f0234334 README.text
e7c8b3f9f63eae1996255031fda32f0b abstract.tex
a877c0679f92f024fd39dfed4a7a4b15 aecthesis.cls
a6595f75abde670010e4a93f463b9031 algorithm.txt
774b09eb7615caad39d43f62e88dc25a appa.aux
43503483dd1aa5ea293b7856784c79fa appa.tex
ce9a06c1434def4c86402e8e5955f261 appb.aux
2f2ec168b2f116a3d18ac911c0f8b4e9 appb.tex
ca1b6b5a2817f608f38942657b675e44 biblio.aux
7cbfe9ab13027794772d2c720bf3ba1a biblio.tex
b0867317b480acdc47c7dd6dde5e32cb bibliography.bib
d5b81523a1315a56d03ce251b7f331c6 chap1.aux
d4edaaceab1cf059dd6d94c6e4599ae4 chap1.tex
4a80ddddcf9e630e9a63a6d441d36dd7 chap2.aux
590fd3b7783975dd0847c1d7dbf92b04 chap2.log
918daf9d95273d5ba86c04b87107b50a chap2.tex
e82b7f2e02917afc6f4467c1ab453a4d chap3.aux
d067477e6d4689d4f02feb5bed15f172 chap3.tex
ea79fb164f54d8f47da821fabca2154e chap4.aux
f74dd2fc449d93c711593a62cdbebfd0 chap4.tex
be38e142aad1fb7ce3dc480a4364b81a chap5.aux
d41d8cd98f00b204e9800998ecf8427e chap5.tex
10efe83a89d7fbc2026aed1ff10b2c56 code/.DS_Store
fe6f39d829a56849db68cfd49888f1b8 code/dataset-to-topology.py
e806183f41b58249c7d45b412dcb2d1f code/random-topo-generator.py
c4f926eed025a4f5f0333332c0ca47dd conclusion.aux
3303dd283bfc410520cf8e4f0f665310 conclusion.tex
8d4864976595476e8ad6fadd7a9123ba contents.aux
2b92d846df905598dd5f1699b9cfbbdb contents.tex
2ce336d84b3b42b1d8ce2ed7b3dfec3d cover.aux
265e11e123033adbc09c180e0ea4b8cd cover.tex
02e998bc04109bfa9bec0db4e47e6854 graphics/.directory
92496f42647902a81644510f5e06c158 graphics/.DS_Store
2d048625691dc4228b4ae2bb48ce5f77 graphics/ASACM-controller.png
7db1c22d7d632070d3177630cbe3a4ea graphics/ASACM.png
05979987086ea24cb9895849c4bab549 graphics/Assam_Engineering_College_Logo.jpg
b079b92683e98a3b394eed50dfc273ee graphics/dataset-topo-gen-cli.png
7c7e540355dc40c077372ac229c19b56 graphics/dataset-topo-gen-mininet.png
998a20fca04b3d16644b4f4caaf102f2 graphics/dataset-topo-gen-save.png
b0a88340bfb1c8a68b26e858030a12d1 graphics/iitglogo-eps-converted-to.pdf
7a0d6918e3a650fd1efdef83eb69f13a graphics/iitglogo.eps
245e1dd529df8ec57bcefb07c8c8886f graphics/inter-dc.png
e87d5d2430a3fe7d5ac992035e3719fc graphics/inter-tech-load-balancing.png
45be7a28f91abe33a02ee2c6ebed2c03 graphics/message-format.png
fc731e65be23733544b75e7252584a5b graphics/network.png
84306bf328b0822cea35f93b2f0d1fce graphics/OpenFlow-Diagram-cropped.jpg
6d4ada9ad6ca5dc2105daaaf1664041e graphics/OpenFlow-Diagram.jpg
e78100a33bf5541779262ef59f2b8015 graphics/OpenQoS-controller.png
7a14130aecaa55507fa6c56a2945dfbb graphics/OpenQoS-flow-identification.png
fca8face83770117efc259fc98ae9ccb graphics/OpenQoS-flow-table-pipeline.png
9b23c15ae9c04978cdfd69b21122c188 graphics/reservation-algorithm.png
dc85d7c38fa756ccf9cc69f0ffae3f4b graphics/SDN-architecture-overview-transparent.png
af4625335e1e6da9506c99d77191c710 graphics/snapshot62.png~
21522008367d859350c55b07e2fde7c5 graphics/snapshot63.png
e80cab49696260d8e42dcf038ea0fb8c graphics/snapshot64.png
168258dc414dce5eecc835de44287faf graphics/snapshot65.png
c6b6ebfb596a5599359fc7f6ca37eab5 graphics/snapshot66.png
9c199c6e759114729ea3d40358cdda93 graphics/snapshot67.png
fde57f32ad2e89833f034546bf14bb60 graphics/snapshot68.png
c0f010f1cd9e1a630cc73efe19e1c888 graphics/snapshot69.png
8c9d7d9dc30951f8e26db4669e581663 graphics/wpid-wp-1437832561820.jpeg
ea74beead1aa2b711ec2669ba60562c3 lgrind.sty
478683c30e5fb30e8c73e24d625e688e main.aux
68c222b17a3a2333f2f722b9f8bd7939 main.bbl
847e5c7d09cb5fc59931f03e1074f69d main.bib
fd1ba72f07a565a0055b5a088fd981b9 main.bib.info
6388325491dde99b8516ebb0a5c209f6 main.blg
e3149428f4256ac6cae07fdc7fc01e66 main.lof
6e9acb1d448bb844b3d22c3d8d90ea8a main.log
104a8a462b27a2267fd07b368245cdd0 main.lot
6c454ac824c2e9bb70f6912ad9d02fb2 main.pdf
9514c7f66f8bebd0acca87241d92f32b main.synctex.gz
7a8d74bf211245a6c1afcad8b65d96ac main.tex
5798f4990a1ecd31fcf42abf911122de main.toc
060f4681619ce98af3e898967af1f97e mitthesis.cls
fc731e65be23733544b75e7252584a5b network.png
81c7974f942d201a4e6c95c575e356a1 propcover.tex
bc7b71cde9afaaa8a27b3043aa6043d3 ref.bib
1c5abb307c4829502a28814b3a42d384 signature.tex
61d4c40fd0c43a537fcbe532bc8726bf texput.log
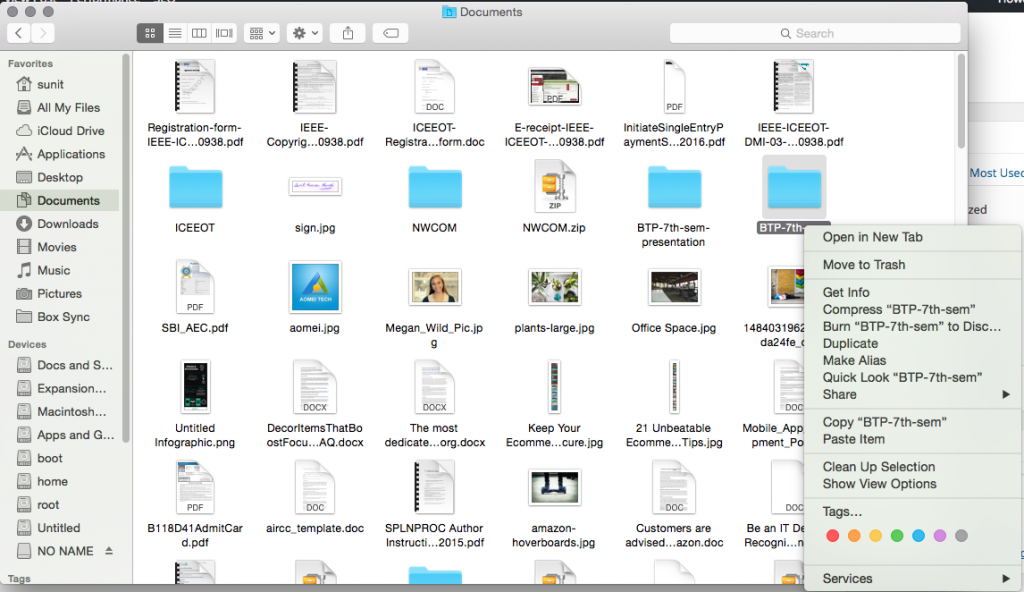
Then I delete the folder.
I then run a disk scan to locate my deleted folder, and soon afterwards searching the name, the the lost folder is found.
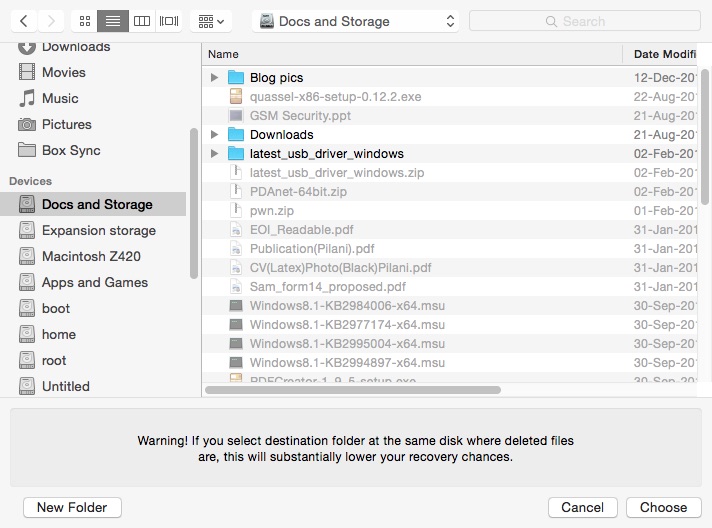
I proceed to restore the folder and it asks me to choose a save location.
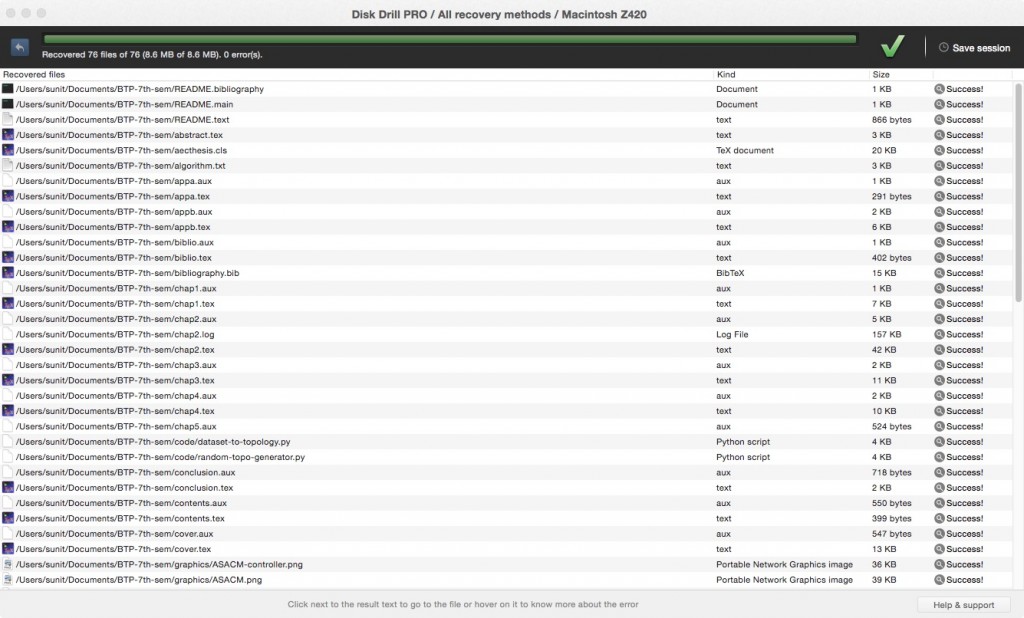
The recovery process completes with no errors reported.
Then I navigate to the saved location and run the MD5 checksum again:
blsz420nandifamilyin:BTP-7th-sem sunit$ cd /Volumes/Docs\ and\ Storage/Users/sunit/Documents/BTP-7th-sem/
blsz420nandifamilyin:BTP-7th-sem sunit$ find * -type f -exec md5 -r '{}' \;
10288f0a52de797cf30baa6d181cb5af README.bibliography
8a681eb41e84b72cd311b389cc05220f README.main
8063de1459364ee3d044b027f0234334 README.text
10288f0a52de797cf30baa6d181cb5af README1.bibliography
8a681eb41e84b72cd311b389cc05220f README1.main
8063de1459364ee3d044b027f0234334 README1.text
e7c8b3f9f63eae1996255031fda32f0b abstract.tex
e7c8b3f9f63eae1996255031fda32f0b abstract1.tex
a877c0679f92f024fd39dfed4a7a4b15 aecthesis.cls
a877c0679f92f024fd39dfed4a7a4b15 aecthesis1.cls
a6595f75abde670010e4a93f463b9031 algorithm.txt
a6595f75abde670010e4a93f463b9031 algorithm1.txt
774b09eb7615caad39d43f62e88dc25a appa.aux
43503483dd1aa5ea293b7856784c79fa appa.tex
774b09eb7615caad39d43f62e88dc25a appa1.aux
43503483dd1aa5ea293b7856784c79fa appa1.tex
ce9a06c1434def4c86402e8e5955f261 appb.aux
2f2ec168b2f116a3d18ac911c0f8b4e9 appb.tex
ce9a06c1434def4c86402e8e5955f261 appb1.aux
2f2ec168b2f116a3d18ac911c0f8b4e9 appb1.tex
ca1b6b5a2817f608f38942657b675e44 biblio.aux
7cbfe9ab13027794772d2c720bf3ba1a biblio.tex
ca1b6b5a2817f608f38942657b675e44 biblio1.aux
7cbfe9ab13027794772d2c720bf3ba1a biblio1.tex
b0867317b480acdc47c7dd6dde5e32cb bibliography.bib
b0867317b480acdc47c7dd6dde5e32cb bibliography1.bib
d5b81523a1315a56d03ce251b7f331c6 chap1.aux
d4edaaceab1cf059dd6d94c6e4599ae4 chap1.tex
d5b81523a1315a56d03ce251b7f331c6 chap11.aux
d4edaaceab1cf059dd6d94c6e4599ae4 chap11.tex
4a80ddddcf9e630e9a63a6d441d36dd7 chap2.aux
590fd3b7783975dd0847c1d7dbf92b04 chap2.log
918daf9d95273d5ba86c04b87107b50a chap2.tex
4a80ddddcf9e630e9a63a6d441d36dd7 chap21.aux
590fd3b7783975dd0847c1d7dbf92b04 chap21.log
918daf9d95273d5ba86c04b87107b50a chap21.tex
e82b7f2e02917afc6f4467c1ab453a4d chap3.aux
d067477e6d4689d4f02feb5bed15f172 chap3.tex
e82b7f2e02917afc6f4467c1ab453a4d chap31.aux
d067477e6d4689d4f02feb5bed15f172 chap31.tex
ea79fb164f54d8f47da821fabca2154e chap4.aux
f74dd2fc449d93c711593a62cdbebfd0 chap4.tex
ea79fb164f54d8f47da821fabca2154e chap41.aux
f74dd2fc449d93c711593a62cdbebfd0 chap41.tex
be38e142aad1fb7ce3dc480a4364b81a chap5.aux
be38e142aad1fb7ce3dc480a4364b81a chap51.aux
fe6f39d829a56849db68cfd49888f1b8 code/dataset-to-topology.py
fe6f39d829a56849db68cfd49888f1b8 code/dataset-to-topology1.py
e806183f41b58249c7d45b412dcb2d1f code/random-topo-generator.py
e806183f41b58249c7d45b412dcb2d1f code/random-topo-generator1.py
c4f926eed025a4f5f0333332c0ca47dd conclusion.aux
3303dd283bfc410520cf8e4f0f665310 conclusion.tex
c4f926eed025a4f5f0333332c0ca47dd conclusion1.aux
3303dd283bfc410520cf8e4f0f665310 conclusion1.tex
8d4864976595476e8ad6fadd7a9123ba contents.aux
2b92d846df905598dd5f1699b9cfbbdb contents.tex
8d4864976595476e8ad6fadd7a9123ba contents1.aux
2b92d846df905598dd5f1699b9cfbbdb contents1.tex
2ce336d84b3b42b1d8ce2ed7b3dfec3d cover.aux
265e11e123033adbc09c180e0ea4b8cd cover.tex
2ce336d84b3b42b1d8ce2ed7b3dfec3d cover1.aux
265e11e123033adbc09c180e0ea4b8cd cover1.tex
84306bf328b0822cea35f93b2f0d1fce graphics/OpenFlow-Diagram-cropped.jpg
84306bf328b0822cea35f93b2f0d1fce graphics/OpenFlow-Diagram-cropped1.jpg
97116ebe0a694d8aee91766ed08fca1c graphics/OpenFlow-Diagram.jpg
97116ebe0a694d8aee91766ed08fca1c graphics/OpenFlow-Diagram1.jpg
e78100a33bf5541779262ef59f2b8015 graphics/OpenQoS-controller.png
e78100a33bf5541779262ef59f2b8015 graphics/OpenQoS-controller1.png
7a14130aecaa55507fa6c56a2945dfbb graphics/OpenQoS-flow-identification.png
7a14130aecaa55507fa6c56a2945dfbb graphics/OpenQoS-flow-identification1.png
9b23c15ae9c04978cdfd69b21122c188 graphics/reservation-algorithm.png
9b23c15ae9c04978cdfd69b21122c188 graphics/reservation-algorithm1.png
dc85d7c38fa756ccf9cc69f0ffae3f4b graphics/SDN-architecture-overview-transparent.png
dc85d7c38fa756ccf9cc69f0ffae3f4b graphics/SDN-architecture-overview-transparent1.png
af4625335e1e6da9506c99d77191c710 graphics/snapshot62.png~
af4625335e1e6da9506c99d77191c710 graphics/snapshot621.png~
21522008367d859350c55b07e2fde7c5 graphics/snapshot63.png
21522008367d859350c55b07e2fde7c5 graphics/snapshot631.png
1af1a39ba192fbd6d1a99b77df28a6e7 graphics/snapshot64.png
1af1a39ba192fbd6d1a99b77df28a6e7 graphics/snapshot641.png
168258dc414dce5eecc835de44287faf graphics/snapshot65.png
168258dc414dce5eecc835de44287faf graphics/snapshot651.png
c6b6ebfb596a5599359fc7f6ca37eab5 graphics/snapshot66.png
c6b6ebfb596a5599359fc7f6ca37eab5 graphics/snapshot661.png
9c199c6e759114729ea3d40358cdda93 graphics/snapshot67.png
9c199c6e759114729ea3d40358cdda93 graphics/snapshot671.png
fde57f32ad2e89833f034546bf14bb60 graphics/snapshot68.png
fde57f32ad2e89833f034546bf14bb60 graphics/snapshot681.png
8c9d7d9dc30951f8e26db4669e581663 graphics/wpid-wp-1437832561820.jpeg
07b90e44327761001f0ca48147c2a510 graphics/wpid-wp-14378325618201.jpeg
2d048625691dc4228b4ae2bb48ce5f77 graphics/ASACM-controller.png
2d048625691dc4228b4ae2bb48ce5f77 graphics/ASACM-controller1.png
7db1c22d7d632070d3177630cbe3a4ea graphics/ASACM.png
7db1c22d7d632070d3177630cbe3a4ea graphics/ASACM1.png
05979987086ea24cb9895849c4bab549 graphics/Assam_Engineering_College_Logo.jpg
05979987086ea24cb9895849c4bab549 graphics/Assam_Engineering_College_Logo1.jpg
b079b92683e98a3b394eed50dfc273ee graphics/dataset-topo-gen-cli.png
b079b92683e98a3b394eed50dfc273ee graphics/dataset-topo-gen-cli1.png
7c7e540355dc40c077372ac229c19b56 graphics/dataset-topo-gen-mininet.png
7c7e540355dc40c077372ac229c19b56 graphics/dataset-topo-gen-mininet1.png
998a20fca04b3d16644b4f4caaf102f2 graphics/dataset-topo-gen-save.png
998a20fca04b3d16644b4f4caaf102f2 graphics/dataset-topo-gen-save1.png
b0a88340bfb1c8a68b26e858030a12d1 graphics/iitglogo-eps-converted-to.pdf
b0a88340bfb1c8a68b26e858030a12d1 graphics/iitglogo-eps-converted-to1.pdf
7a0d6918e3a650fd1efdef83eb69f13a graphics/iitglogo.eps
7a0d6918e3a650fd1efdef83eb69f13a graphics/iitglogo1.eps
245e1dd529df8ec57bcefb07c8c8886f graphics/inter-dc.png
245e1dd529df8ec57bcefb07c8c8886f graphics/inter-dc1.png
e87d5d2430a3fe7d5ac992035e3719fc graphics/inter-tech-load-balancing.png
e87d5d2430a3fe7d5ac992035e3719fc graphics/inter-tech-load-balancing1.png
45be7a28f91abe33a02ee2c6ebed2c03 graphics/message-format.png
45be7a28f91abe33a02ee2c6ebed2c03 graphics/message-format1.png
e5f99c4d5d844a5430ea79a39a692b92 graphics/network.png
e5f99c4d5d844a5430ea79a39a692b92 graphics/network1.png
ea74beead1aa2b711ec2669ba60562c3 lgrind.sty
ea74beead1aa2b711ec2669ba60562c3 lgrind1.sty
478683c30e5fb30e8c73e24d625e688e main.aux
68c222b17a3a2333f2f722b9f8bd7939 main.bbl
847e5c7d09cb5fc59931f03e1074f69d main.bib
fd1ba72f07a565a0055b5a088fd981b9 main.bib.info
fd1ba72f07a565a0055b5a088fd981b9 main.bib1.info
6388325491dde99b8516ebb0a5c209f6 main.blg
e3149428f4256ac6cae07fdc7fc01e66 main.lof
6e9acb1d448bb844b3d22c3d8d90ea8a main.log
104a8a462b27a2267fd07b368245cdd0 main.lot
fec176d201a2328eb4d92b54eb90551c main.pdf
9514c7f66f8bebd0acca87241d92f32b main.synctex.gz
9514c7f66f8bebd0acca87241d92f32b main.synctex1.gz
7a8d74bf211245a6c1afcad8b65d96ac main.tex
5798f4990a1ecd31fcf42abf911122de main.toc
478683c30e5fb30e8c73e24d625e688e main1.aux
68c222b17a3a2333f2f722b9f8bd7939 main1.bbl
847e5c7d09cb5fc59931f03e1074f69d main1.bib
6388325491dde99b8516ebb0a5c209f6 main1.blg
e3149428f4256ac6cae07fdc7fc01e66 main1.lof
6e9acb1d448bb844b3d22c3d8d90ea8a main1.log
104a8a462b27a2267fd07b368245cdd0 main1.lot
fec176d201a2328eb4d92b54eb90551c main1.pdf
7a8d74bf211245a6c1afcad8b65d96ac main1.tex
5798f4990a1ecd31fcf42abf911122de main1.toc
060f4681619ce98af3e898967af1f97e mitthesis.cls
060f4681619ce98af3e898967af1f97e mitthesis1.cls
fc731e65be23733544b75e7252584a5b network.png
fc731e65be23733544b75e7252584a5b network1.png
81c7974f942d201a4e6c95c575e356a1 propcover.tex
81c7974f942d201a4e6c95c575e356a1 propcover1.tex
bc7b71cde9afaaa8a27b3043aa6043d3 ref.bib
bc7b71cde9afaaa8a27b3043aa6043d3 ref1.bib
1c5abb307c4829502a28814b3a42d384 signature.tex
1c5abb307c4829502a28814b3a42d384 signature1.tex
61d4c40fd0c43a537fcbe532bc8726bf texput.log
61d4c40fd0c43a537fcbe532bc8726bf texput1.log
The original files were backed up to a different drive before they were deleted so, we can test if there is any change in the files by using the diff utility comparing the checksums:
blsz420nandifamilyin:~$ cd /Volumes/Expansion\ storage/BTP-7th-sem/
blsz420nandifamilyin:BTP-7th-sem sunit$ find . -type f -exec md5 -r '{}' \; > /Users/sunit/md5sums.txt
blsz420nandifamilyin:BTP-7th-sem sunit$ cd /Volumes/Docs\ and\ Storage/Users/sunit/Documents/BTP-7th-sem/
blsz420nandifamilyin:BTP-7th-sem sunit$ find . -type f -exec md5 -r '{}' \; > /Users/sunit/md5sums-2.txt
blsz420nandifamilyin:BTP-7th-sem sunit$ cd /Users/sunit/
blsz420nandifamilyin:~ sunit$ diff md5sums.txt md5sums-2.txt
blsz420nandifamilyin:~ sunit$
The diff command doesn’t return anything which means the checksums of files in both the directories match. This clearly verifies that Disk Drill has successfully managed to recover the file even after it was deleted. We can therefore, believe that this app works as we’d expect it to.
Apart from HFS and HFS+, the other filesystems from which Disk Drill can recover are FAT16, FAT32, exFAT, NTFS, EXT3 and EXT4, making it a more complete solution compared to other data recovery tools in the market. Most recovery utilities for Windows and Macs conveniently ignore Linux filesystems, but this isn’t the case with Disk Drill.
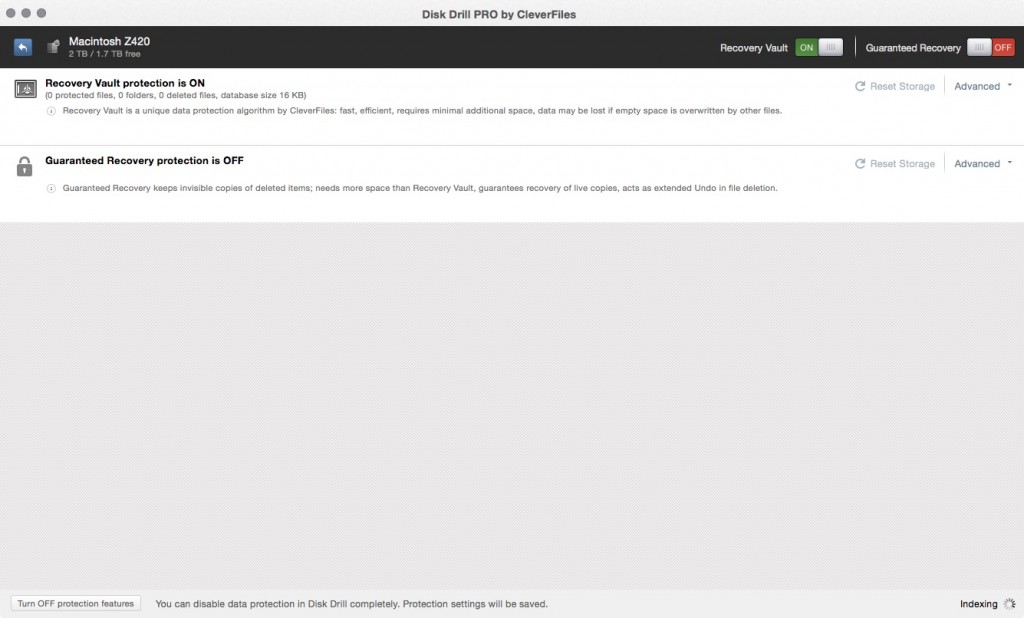
Apart from data recovery, Disk Drill offers a hot backup option for the drive on which OSX is installed. Clicking ‘Protect’ in the OS drive in the main menu gives you two options, namely Recovery Vault and Guaranteed Recovery. Recovery Vault is a simple file-system snapshot scheme and saves changes to files incrementally to a database so that lost files or changes can be rolled back later. Guaranteed Recovery, on the other hand is a file mirroring scheme that saves copies of files on the disk space to other locations. And as you’d expect, Guaranteed Recovery is more reliable but comes at the cost of disk space.
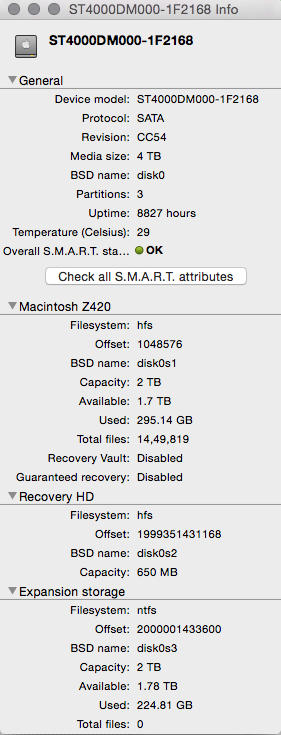
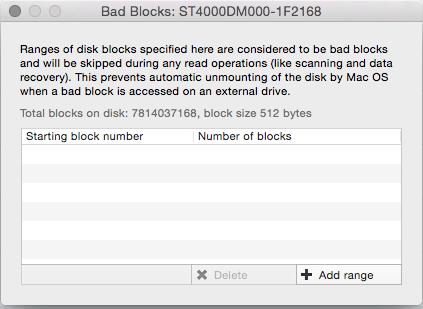
Finally one can use the ‘Extras’ menu to export your drives as dmg images (drive imaging), to get info about the drive and specify bad blocks if it is a storage device.
There is even a ‘data map’ feature that lists the disk usage of files in a descending space consumption usage order.
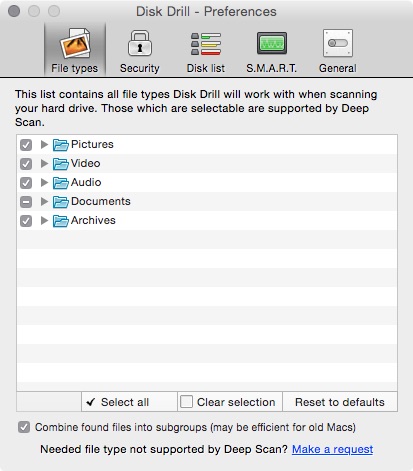
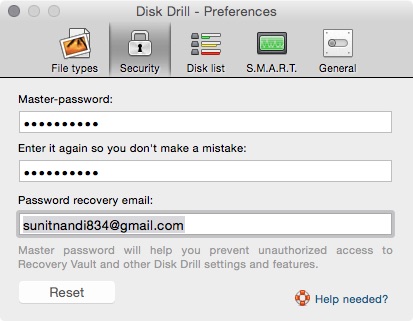
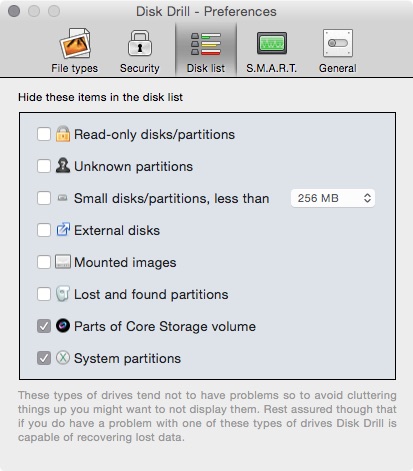
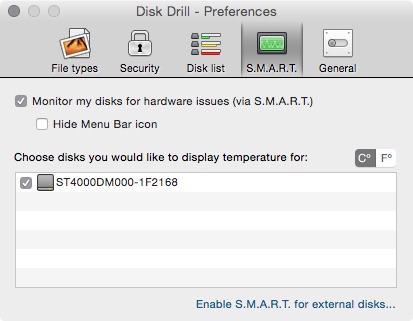
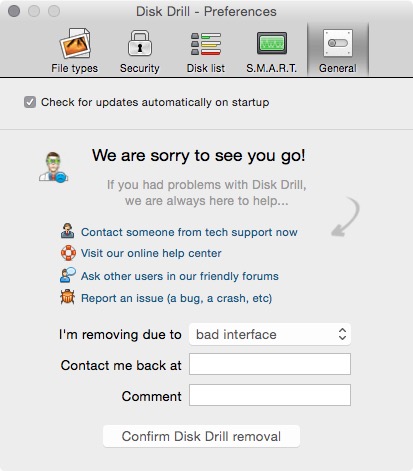
Disk Drill’s Preferences menu, allows you to choose the file types you wish to recover, a secure mechanism to lock access, gives you ability to hide/show partitions according to type, configure S.M.A.R.T. status to be shown on the MenuBar and a general section that toggles the ability of the app to check for updates and also allows complete removal of the app from the system.
The interface is well laid out and very straightforward to use. The app seems to be rock solid and pretty mature, as I could not find any sort of minor quirks. I can definitely recommend this to any Mac user who wishes to take care of their files and recover from unforeseen circumstances like accidental deletion, data corruption or drive failure.
Summary
Pros
- Very comprehensive file and partition recovery with variety of options
- Complete support for HFS, HFS+, FAT16, FAT32, NTFS, EXT3 and EXT4
- Easy to use UI
- Data recovery is effective as verified in our tests
- Ability to protect your OSX drive from data loss by using snapshotting (Recovery Vault) and multiple copies of files (Guaranteed Recovery)
- Ability to view disk usage
- Ability to backup drives into DMG files
Cons
None so far.
Getting for yourself
Disk Drill is downloadable from here. The basic version actively monitors your drive and saves you from accidental file deletion. However, for recovery of lost files (files lost before Disk Drill was installed or files lost when the app is off) requires one to buy the Pro edition for $89 (which includes installation on upto 3 Macs). One can also buy the Enterprise Edition (installation on unlimited no. of Macs) for companies and institutions for $399.
Conclusion
Disk Drill Pro is an effective data recovery tool for Mac OSX users whether novice or expert. It works perfectly, supports all popular filesystems and provides ample active measures to prevent data loss. We can happily recommend this product to our readers.


1 Comment
Mubasshir
14 February, 2016I have experience of using this user friendly software. I accidentally deleted one 4 GB file from my hard drive. My brother recommended me to use Disk Drill. Though I never use data recovery software before, but I was able to recover easily by this software.
This software supports for HFS, HFS+, FAT16, FAT32, NTFS, EXT3 and EXT4 and very useful for lost partition recovery. I found later that the data recovery speed is faster than most of the data recovery software. But video recovery rate should be more faster. The quick and deep scan function is also very useful to fix normal malware issues.
This is a software where you have the full control of recovery system to you.