Internet is the hottest trend which is prevailing for more than a decade and is one of the most important parts of everyone’s life. It has changed our lives massively and is also affecting our lifestyle. It includes many benefits which is important to us and makes our life easier than before. But is it truly a friend? Or a stranger who can make someone’s life miserable?
While people are busy posting their day to day activities on social media, there are some criminals who are secretly gathering sensitive information, which maybe financial or personal. Hacking is a worldwide phenomenon which is not so difficult to perform and in the process, the hackers can obtain tons of information in just few seconds. Thus keeping your data and information safe and away from those criminal minds is a necessity. Some ideas are given below which a user may apply-
Protecting Your Credit Cards
Purchasing goods online is easy and less tiring. But while buying online, it must be ensured that the credit card information must be secured and protected by the website. While buying it should be ensured that the URL starts with “HTTPS”, and not simply “HTTP”. Purchasing from an unsecured network may lead to trouble as the information can be extracted through various heinous methods. A better idea is to use a prepaid credit card with limited funds for online purchase which can reduce the risk of losing a huge amount of money if the information is stolen. Thus safely handling credit cards is very important.
Safely Using Social Media
Social media is like an addiction to most of us. We spend lots and lots of time updating everything about our daily life. But everything we update may not be as safe as we think it is. Our private data should be only showed to the known ones and should be hidden from the evil world. Our birthday, address, phone numbers should also be hidden from public to prevent the criminals from operating various dangerous works.
To avoid this problem, the security settings should be personalized and every data should be only shared with the trusted ones. This is a major step towards the safety of our information.
Using Cloud for Back-ups
Backing up our important files and data is necessary keeping in mind that our devices can be lost or be stolen anytime. Clouds are used for data storage. For many years cloud is used widely and has become more secured. Large firms like Amazon, Microsoft is using cloud and also healthcare units and hospitals are using it for backing bulk amount of data. Cloud also helps in securing confidential files and having easy access to them.
Google drive and Gmail are common examples of this software. They helps us to store and upload files and can be accessed from anywhere around the world where internet connection can be accessed.
Protecting Password
Passwords are essential for any email account. Any password should not be easy to interpret like numbers, birthdays, etc or else some known people can also take advantage and can get access to your personal data. Also everyone should sign out from their email account or from any social media website after surfing at any cyber café or someone else’s computer.
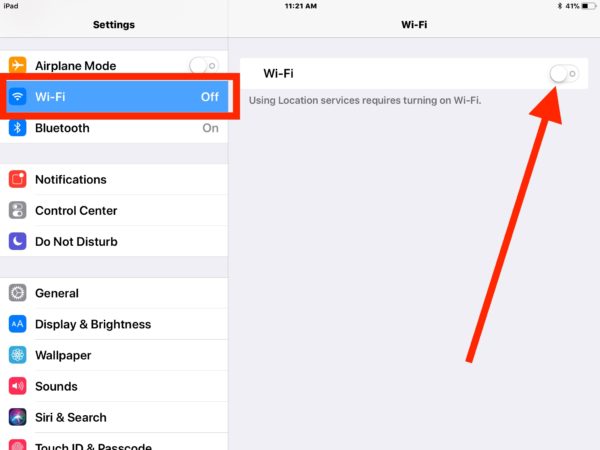
Disable Bluetooth and WiFi when not in use
Bluetooth and WiFi are very useful but also can prove to be a problem if not turned off while not in use. Other devices in the vicinity can get access to our data. It can also get access to our open file sharing networks. Thus when Bluetooth and WiFi are not in use, they should be turned off.
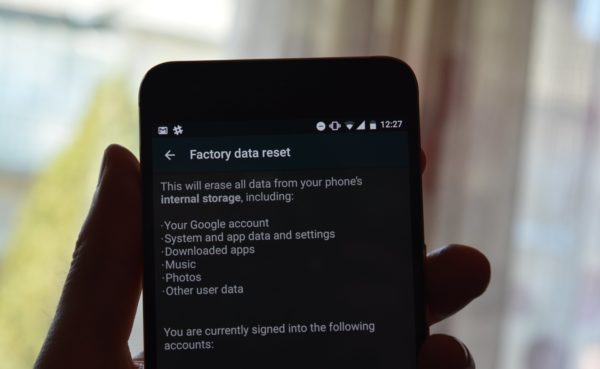
Factory Reset
When we sell our previous laptop or any devices, deleting our files will not do the work alone. It will not permanently erase our data from the machine. Thus before selling or throwing away our old machines, we must make sure that the machine is given a factory reset and the drives are fully wiped or else our data and files will be open to others and our personal documents will not remain personal anymore. Now there are online sites that can help you find how to remove your information from the internet and secure your information from hackers.
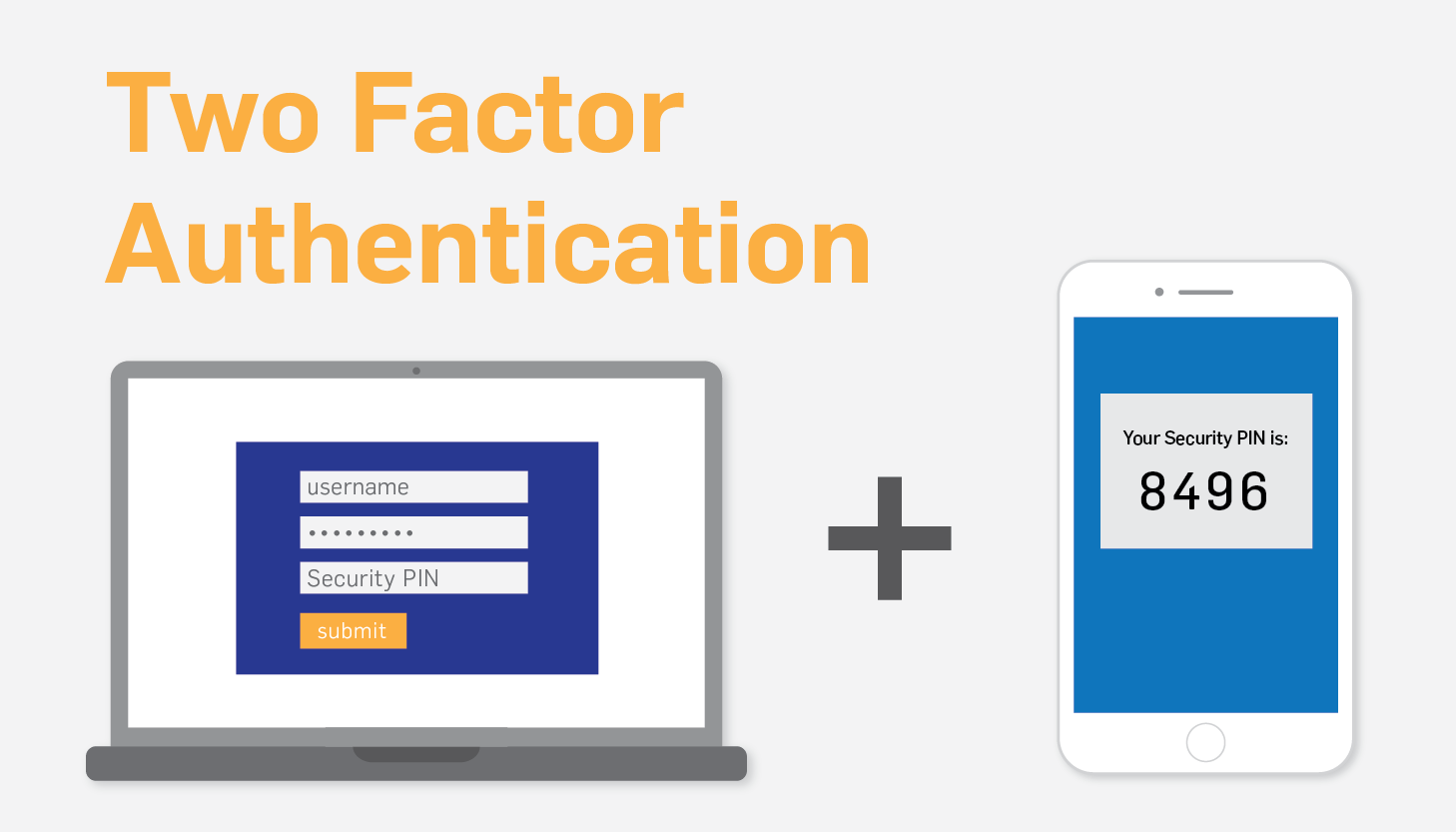
2-Step Authentication
2-step authentication is used to make our account more secure. Large companies like Google, Facebook offer 2-step authentication. It asks the users to enter a code sent to their mobile device in order to sign in. This is a more secure operation. Other companies will only ask for email address or mobile number to sign in. An advantage of this system is that if someone is trying to sign in from another device, it will send a message to the registered number asking for verification. This system provides extra security for our information.
Thus taking these measures to keep our files and data safe on internet is necessary. Ethical hackers should be given hacking certification to fight against the criminal hackers and create new software and programs to keep our data safe and make our internet experience better and better.