The bane of every interaction with the Internet is usernames and passwords. We all have had situations where we thought we had the right password, yet it failed. Every secure website requires a username and a password. When we first started using computers, we would try to use and reuse the same login credentials until a new username or password requirement forced a modification or change. Over time, this started to give us all problems, for we soon started writing the passwords down, used a computer-based document, or started to utilize a password manager.
In the corporate world, businesses can be compromised by their users’ home computers and IT devices whenever remote access is allowed. Therefore, comprehensive corporate password and security policies must apply to all the computers and devices employees have, including phones, tablets, home routers, and VPNs.
Baltimore IT support professional, Keith Marchiano with Kyocera Intelligence shares important policies you need, including acceptable password managers.
Understanding the Issues
Passwords are only as strong as their weakest use within an organization.
- People like to have easy to use or access login credentials:
- Employees want quick access to passwords they have forgotten.
- They don’t like to use easy-to-forget strong passwords.
- People like cross-platform autofill password managers. They want the password manager to work on all the platforms they use: iOS, MacOS, Android, Windows, Linux, etc. The manager needs to work with their favorite browsers.
- They seldom consider how solid or secure the password manager itself is, unless it is corporately approved and its use enforced. They trust the advertising about it.
- Multi-factor authentication is often considered another waste of time. It is especially annoying when the second factor is somehow unavailable.
- If only one person is sloppy or unwise with password or computing device use, the entire enterprise could be at risk:
- Is that person susceptible to phishing attacks?
- Does that person write down the passwords onto easily located pieces of paper?
- Are the chosen passwords simple dictionary words easy to guess?
- Password management risks are greatly compounded if any employees work in a home office, at a field office, or from a laptop at a customer site.
- Hackers could append malware on even your most trusted software through phishing attacks. Any software installed on a computer from the Internet could become infected with malware, installing backdoors that hackers could use to bypass normal login credentials.
Hardware with passwords, especially routers and firewalls at any level of the corporate Intranet or Internet, at work, in the field, or at home, could potentially pass your information to groups hostile to your enterprise. Once the information is off your computers, hackers can spend all the time they want to find the correct keys to unlock your data.
Really Only Two Types of Passwords
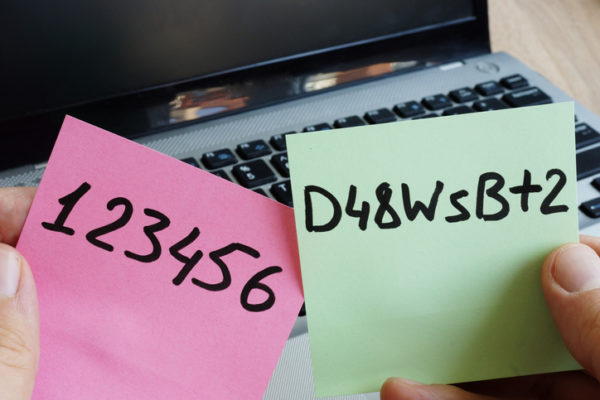
Passwords should be considered as either weak or strong. The idea of intermediate or medium strength is flawed because it fails to take into account that most hacking attacks succeed with just a little extra time spent on the difference.
A weak password utilizes standard dictionary words, reused passwords, parts of login credentials, or information a hacker may quickly discover about an intended victim’s personality or personal history. A password may seem to be strong because of length, but if it can be guessed by knowing something about the victim, it becomes weak.
Simply finding a paper note with a password can open up a lot of accounts. Papers in the trash or left on a desk can sometimes give a cyber thief enough information to access critical website accounts. This is a good reason why all IT workers should have fine crosscut paper shredders in their offices and homes.
What Makes a Strong, Secure Password?
Strong passwords should take the hacking resources of a foreign government a minimum of many weeks to break. The most secure passwords have two major characteristics. First, they are long. The longer the password, no matter if it a phrase or gibberish, the better. Second, they could be 15-characters of pure gibberish.
A 32-letter phrase from an obscure poem is both easy to remember and is secure. But if the hacker knows the intended victim well, a phrase may be easy to guess even if it is long. That is why the obscurity factor is important; even the intended victim’s most significant other should not be able to guess that phrase.
Common letters may have numbers or other keyboard symbols substituted for them within a phrase. Irregular uses of capitalization complicate things a bit. Those make dictionary words more difficult for simple dictionary attacks. If the passwords are permitted to have spaces, then those should be irregularly inserted.
A mixture of different human languages makes it more difficult for hacking using a dictionary approach. If someone knows a few words of Japanese, Japanese Kanji can be mixed into the English phrase. The resulting multilingual phrase is still easily remembered by the user but more difficult for hackers. However, Japanese words like sushi or tsunami should not be counted as foreign words since they are regularly used in English.
Secure passwords must not be a combination of previously used passwords and login credentials, nor of information about the victim easily obtained from a Google or other search engine check. More sophisticated dictionary attacks will include those.
The second method of making secure gibberish-like passwords renders them nearly impossible for most users to remember. A combination of at least 15 characters, both upper- and lower-case letters, numbers, spaces, and keyboard characters are utilized. A password generator, ideally from a company that is unconnected to the company that produces one’s password management software, can produce strong gibberish-like passwords. But regular use of these does need a password manager.
Usernames
Unless a specific person is targeted, most password attacks utilize brute force attacks. One relatively easy way to thwart most brute force password attacks once they are detected is to change login credentials. That forces a complete restart of any brute attack once the hackers know that the login credentials have been changed.
However, changing the usernames can create a lot of problems for both the user and the enterprise if not done correctly. Email addresses usually use those same login names, so everybody who emails that person would have to be successfully notified of the change. A broadcast of the email change may actually notify the hacker things have changed. It takes information technology experts with broad platform experience to handle this approach.
Corporate Policy Issues
A corporate enterprise needs to have an actively enforced cybersecurity plan. All employees need to be trained about the plan and then periodically audited for plan compliance. As issues develop, employees and staff need information updates and periodic plan reviews. Nobody with access to the corporate Intranet should ever be exempt from those reviews.
A business enterprise needs to have account access specialists available who understand the best and most current cybersecurity practices. They should have some training in ethical hacking, so they could periodically check the integrity of various links of the organization, including performing phishing-like attacks against new and older employees.
Password Management Technology
There are dozens of password manager software solutions on the market. It takes a lot of research to find out which one is best for each company. Some of the best can be scaled for a corporation. Others are aimed at a single computer or person.
All decent software management programs will create strong gibberish passwords. Some have corporate IT settings for centralized control. The programs vary in terms of how frequently they will force password changes and how smoothly they will integrate with non-browser-based applications.
Many people at home will trust Google or Microsoft to keep their browser passwords. Does the corporation want its employees to access their corporate computers using browser-based password management systems? While they are getting better all the time, those systems still occasionally have problems.
Norton has an excellent password management system integrated with malware and virus detection. It also has an exclusive VPN capability. 1Password also performs many of the same functions as Norton. A nice feature for both is that their corporate user licenses could include their employee’s entire family and all of their personal devices.
But there are some questions seldom addressed by users of password management programs. Whether Huawei is truly an agent of the Chinese military or not, is it not likewise possible that password managing programs and VPNs may also be the products of organizations or governments hostile to your accounts and corporation? This is a very important piece of information usually forgotten in software reviews.
- Who authored that software?
- Where is the software company based? That is sometimes not easy to find!
- Does that software company outsource critical modules of its software?
- Do they make use of software engineers from countries you do not trust?
How A Managed IT Services Company Can Help
A trusted managed IT services provider can assist high-profile people and business enterprises through having and keeping highly-trained specialists. Few companies can afford to keep a certified ethical hacker on their staff, whereas a managed IT services company would consider that person as essential.
They have cloud-computing specialists, who understand the strengths and weaknesses of both corporate on-site technology infrastructures and cloud-based ones. If a hybrid approach would work best, they would have the expertise to balance things for your needs. There may be solid reasons to have a password manager that exclusively works on one device, and they would know.
The company could also investigate all your software solutions. When critical software requires security patches, they will develop the best approaches to roll out those patches to all employees. It is really awkward when new software updates break user login credentials.
The IT company could also audit the home IT environments of home-office employees. Do the employees have active firewalls and proper anti-malware systems in place? Are their smartphones and tablets properly secured? Do they keep their computer systems properly secure, both physically and with approved, updated software? Do they have and use paper quality paper shredders?
Off-site disaster recovery prevention and recovery assistance are other functions for a managed IT services provider. They can make sure that both data and work is properly backed up. They can test the recovery of certain information regularly to make sure no critical parts are missing. Since backup information is encrypted, key employees need to know how to utilize the requisite password credentials.
They can also provide helpdesk assistance for the client’s employees concerning password management, malware, and phishing protection. Your trusted managed IT services provider can help provide you that extra help 24-7.
Companies become best in their class when they spend the most time doing what makes them unique. It is well worth your time and effort to find a trustworthy managed IT services company that can meet your IT needs as your company grows. They will also do the research needed and perform the work, making sure you and your employees have no more password management nightmares.