1. Artificial Intelligence (AI)
The development in technology world has boosted the demand and use of Artificial Intelligence. The Artificial Intelligence can be used for several purposes of development in computer technology because it has the ability to learn and is adaptive in nature.
Artificial Intelligence is used by both security teams and cybercriminals and this makes us think twice for our privacy and security of data and information because attackers can develop a system that learns a data set (Behavior, System Architecture, System Overview) of target, once the attackers system gathers the complete information then this information can be used to develop a model to bypass the target or victim’s security.
The subset of Artificial Intelligence, Machine Learning, is widely used to create more convincing and personalized messages in phishing attacks, which makes easier for attackers to gain the trust of the victim and steal the information and private credentials.
2. Cloud Platforms
All Business and Organizations are shifting towards cloud storage and day-by-day this number is growing rapidly now the fact that people know is cloud platforms are too secure and at some point it is true as these platforms have their own security features but it doesn’t mean that it is completely secure because as the amount and type of access point increases with third party integration, the chances of attackers to attack the system also increases. If the cloud platform is not properly segmented then it is like “A Locker with a Big Hole” where you think your data is safe but attackers very well know how to get your data from that locker.
Cloud-based systems are uniquely vulnerable to DDoS attack, where the servers are loaded with illegitimate traffic by attackers to crash the system and perform their mischievous activity.
Such Attacks are performed on an individual organization or business as a target, but it’s not like only these targeted business and organization suffers with the attack but also all those organizations and businesses get affected that are sharing the resources with target or victim.
The Recent 2019 Report by “Cybersecurity Insiders”
- The top cloud security concerns of cybersecurity professional is data loss and the numbers are too shocking of data loss on cloud platform and it is up to 64%
- The number one spot is taken by “unauthorized access” in cybersecurity of cloud platform which is up to 42% and this unauthorized access are done by insecure APIs, Improper Access and misuse of employee credentials.
The complete report is available here.
3. Crypto-jacking
By the name itself you have got an idea that it is related to Cryptocurrency, and yes it is related to cryptocurrency. As we all know cryptocurrency has become popular and valuable, so making it an appealing target to make money cyber attackers use the technique called crypto-jacking.
Crypto-jacking is illicit mining, which is an easy way for attackers to make profit by using the resources of target for mining and the most shocking part is that it can be easily done under the radar of security system.
You might be wondering how attackers use the resources of victim for mining cryptocurrency. Let me clear the wind, so attackers use malware to get control on the hardware of victim and use their processors, memory and other system hardware for mining.
So attackers, target organizations and businesses because they have big infrastructure of systems that could do mining for them efficiently and this results in too much of a problem for such organizations like System Crash, Spiking Electricity Bills and more.
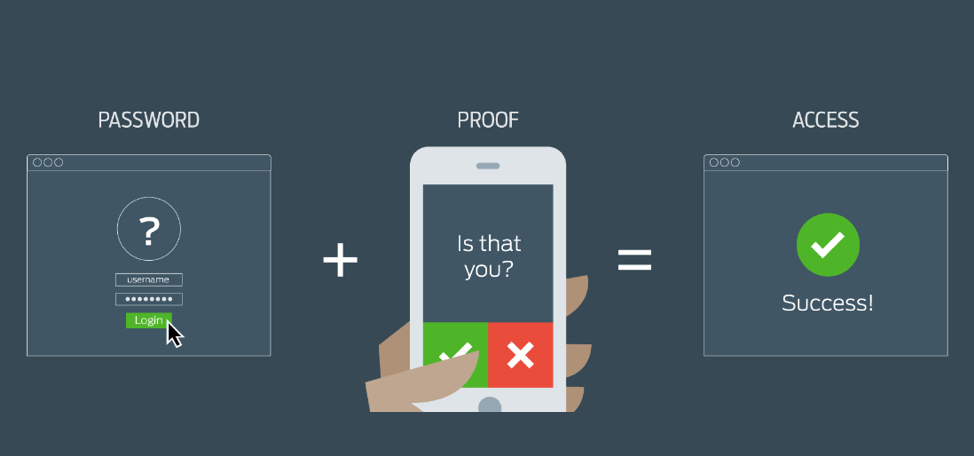
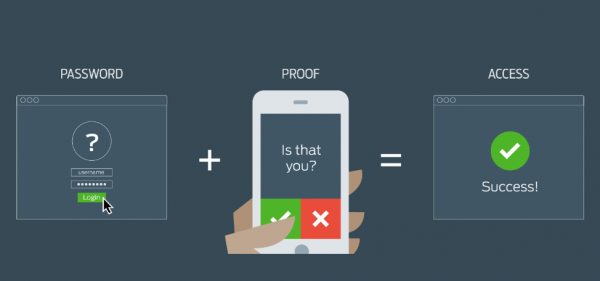
4. Multifactor Authentication
Multifactor authentication is one way that could save you from any type of unauthorized attacks on your data and privacy, but right now the market hasn’t adopted this feature as primary factor of login, so most of the people choose single authentication that is just the password or pin login which could be easily cracked because it is something that is created with limited knowledge of an individual, but two-step authentication like a dongle that generates a temporary password or OTP feature could be much more protective as compared to single step login, now companies and organisation should use multifactor authentication for their every action that requires authentication and login.
4. Operationalizing GDPR
GDPR (General Data Protection Regulation) The European Union has enforced the data protection law for its citizens and every organization and business that want to operate in the European Union need to comply with this regulation and fully meet the requirement of GDPR or else if they don’t meet the security standards of GDPR they will by imposed with fines.
5. IoT
There has been a huge evolution in IoT (Internet of Things) and as the technology world is evolving rapidly, people are adapting to several new technologies in their life, now a days you can see that we have so many devices in our homes and offices that are connected to the internet so all OT (operational Technology) devices can be easily hacked and this could affect your personal life as well as business.
Business and organization are adapting new change in operating by making more use of these smart technologies but let me tell you that IoT devices are not that secured because they haven’t been in the limelight of attack.
According to Statista, by the time 2020 there will be 30 billion connected devices on the internet and the reality is that IT departments have fallen behind to provide the best security to IoT as they often forced to just let these devices connect to the internet without any strong security protocols and attackers get the best deal to steal your data simply by entering into one network which will let them to access all the connected devices over the network and some IoT devices contain personal and sensitive data which could expose your privacy.
Conclusion
So you would have a complete understanding of Cybersecurity Trends and a good piece of information that “what are the cybersecurity trends in 2019-20” and how this would affect you and your business.
It is very important to know what the cybersecurity trends are because only then you will be able to prepare yourself and protect your organization from such attacks.
It is much better if you go for any security agency for your organization protection because only professionals can identify the cause and secure your network.
QLD Managed IT Support Prosnet provides you with the best cyber security support that protects you and your business from any cyber-attack and virus that could give you a nightmare.