Cybercrime is a real threat in today’s day and age. For professional businesses and organisations, data is money. According to Comparitech, data breach and theft are affecting stock prices and company shares, causing an almost half percent decrease in them.
Cybercrime and data theft is on the rise and doesn’t seem to be reducing anytime soon. In fact, Cybercrime is predicted to do a damage of almost $6 trillion annually by the year 2021, as per Comparitech. PWC has reported that cybercrime was the second most reported crime in 2016.
The World Economic Forum (WEF) 2018 Global Risks Report has declared cybersecurity as one of its four key areas.
Large organisations or small businesses, both depend heavily on the internet for their businesses to survive and thrive. And every organisation or business has data in some form or the other on the internet. So it is but natural that an organisation’s data is at risk, and now more than ever, due to the increasing threat of cybercrime. The only way to ensure that your organisation doesn’t fall prey to the predator, that is cybercrime, is protection of your organisation’s data and hardware.
There are many small tips which can go a long way in ensuring that your data stays protected and prevent your organisation from falling prey to cyber crime. Here are some tips for your organisation to keep in mind to prevent data theft or loss.
1. Accessibility
Not all employees of an organisation need access to all the data. Limit the access to data and distribute the access. One person should not have access to all the data and different departments should have access to different data. Maintain a list of accessibility of data. This will help you keep track of who has had access to how much data and track the access details too.
2. Crucial Data
Imagine yourself in a hypothetical situation where your organisation has fallen victim to cyber crime. Now try and establish which data is the most important and crucial to your organisation. Once you have established and identified the most important data of the organisation, check its accessibility and authentication requirements to ensure that it is the most protected data. Commonly referred to as the ‘crown jewels’ of data, the theft of it would cause maximum damage to the company or organisation.
3. Strict Data Policy and Plan
This is something that a lot of companies ignore or miss out on, but it is also one of the most important and effective data protection tactics and works the best when it comes to insider data theft. You should have a strict data protection policy in place and also take strict action in case of breach of this policy. This will ensure that your employees are aware of the repercussions and consequences in case of any kind of violation of the data protection policy or plan.
4. Data Backups
Data backup is extremely important and if you aren’t already doing it, you’re very behind on your data loss prevention policies but it’s time to start now. Get your organisation the best data backup software like Acronis, NovaBackup and other of the likes. Data backups is the step each organisation should take for the post-theft period. If your data is backed up, then you can retrieve and get back your lost data without feeling too helpless without the data.
5. Passwords
Guidelines regarding passwords are usually ignored by a lot people and organisations as well. The tip for passwords is to change them every three to four months and not repeat any of the past or present passwords on any other password protected platforms. This is usually ignored by a lot of people, but if practised, then it can protect your data from getting stolen to a large extent. Make it a part of your data protection policy and make it compulsory for all employees of the organisation to change their passwords every three to four months.
6. Firewalls and Antivirus
A strong firewall and a good antivirus are the basics of IT security in any organisation. Make sure that you have a strong firewall to monitor and regulate the incoming and outgoing internet traffic.
Also called as the ‘last line of defense’ in internet security, an antivirus is necessary to prevent any unwanted traffic, which might be a cyberattack, to get through to your office or commercial space network.
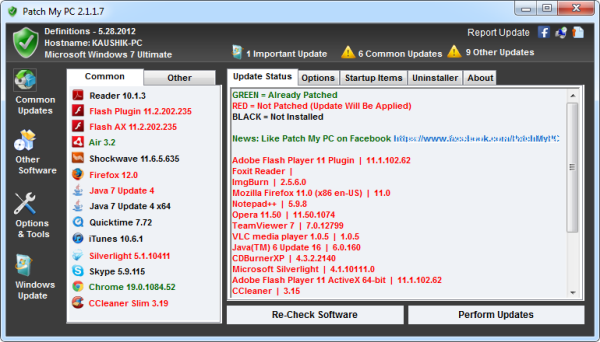
7. Keep Your Softwares and Programmes Updated
If you expect your softwares and programmes to do justice to their functions of protecting your data, then you need to do justice by their updates. Make sure that all your applications are up to date with the recent updates and features because that will ensure that your applications are working well and right.
8. Cybercrime Education
Educate all the members of the organisation on cybercrime and how it takes place. The more the employees understand how cyber attacks work, the more they’ll be careful on their part to ensure that no data theft or loss takes place.
Data security is very important along with hardware security as well. Internet is not the only way to steal data, stealing a laptop or any other hardware of the office which might have important data, can also be equally damaging, in fact more. So here’s what you should do for your IT security as told by IT security product experts Loxit Limited.
1. Visual Surveillance
Put up surveillance cameras to monitor the movements and actions of everyone in the organisation, in areas which have laptops and other machines that belong to the organisation. This will have recorded proof of all that is going on in the organisation and help in prevention and further investigation in case of theft.
2. Locking Up
Probably the easiest and the most underestimated measure of hardware security. Locking up the server room, limiting access to the server room and surveillance will make it difficult for a potential thief to succeed in his/her attempt of thievery.
3. Rack Mount Servers
Rack mount servers are computers which are used as a server and are designed in a way that they can be installed in a framework called a rack. They take up less room, are easier to secure and can be placed and locked into racks, which can then be bolted to the floor. This will make it impossible to move, since it’s bolted to the floor and hence, next to impossible to steal.
Conclusion
Now that hard copies have become soft copies and the past way of doings things on pen and paper have moved on to the internet and laptops, software and virtual data protection is extremely important. However, it is equally important to protect and safeguard the hardware as well. So while you’re taking measures to protect your data from cybercrime, also protect your hardware like laptops from thieves.