Despite numerous ways to protect electronic correspondence, e-mail security remains one of the most serious issues facing both companies and individuals. As soon as you begin to share information electronically, you’re exposed to countless vulnerabilities, experts say. And because e-mail has become so familiar to us, users are willing to share almost anything, from the personal and private all the way to corporate strategies and company secrets. Often without giving security a second thought.
Survey Says
According to a study on cybersecurity trends produced by LinkedIn in 2017, 62% of cybersecurity professionals are moderately confident to not at all confident in their organization’s overall security standards. Only 38% of respondents expressed a high degree of confidence in their organization’s security. The same study noted that while more than half (54%) of security professionals are concerned about protecting sensitive information sent via email, only (12%) believe current e-mail security solutions are effective.
To be sure, there have been many efforts to improve e-mail security, such as Hushmail, Safemail, and for the really ambitious, PGP (Pretty Good Encryption), with its complex system of keys and codes. But all have their limitations and are not easy to implement, especially in a corporate environment, where the idea is to have a standard e-mail address for all employees (such as [email protected]).
E-mail Attacks
Tom Van de Wiele, principal security consultant at F-Secure, says there are many different ways attackers can use e-mail, with such cyber crimes being popular because almost every company relies on e-mail for communication.
“People need to think before they click on attachments and links, but the pressure of many jobs overrides this logic, which attackers understand and exploit,” he said in a report cited by Computer Weekly.
“A successful, secure e-mail strategy depends on a simple and intuitive user experience,” said Prakash Linga, CTO at Vera, in a recent commentary on Helpnet Security. “One that will maintain persistent and dynamic secure, not matter where it travels, and one that can protect confidential communications, classify messages, and be able to change access rights in real time.”
Looking for Answers
Vancouver’s Thierry LeVasseur, an entrepreneur who has a number of patents in the cybersecurity area, is one of those looking to build a better mousetrap for e-mail security.
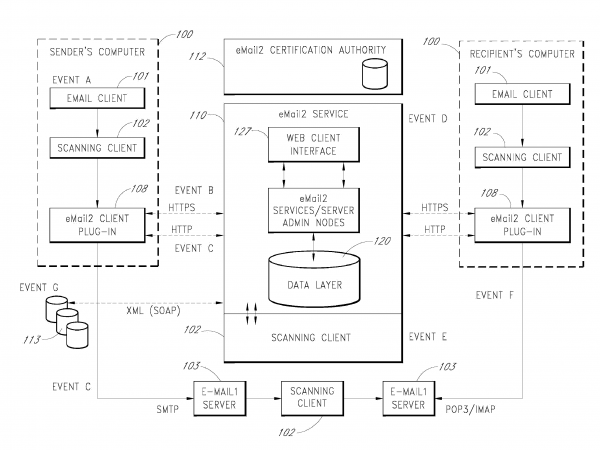
Through a family of patented advances, Thierry LeVasseur, who has 25 years of experience studying web-based issues, has devised what he calls a “comprehensive solution that is compatible with existing systems, but improves their security and functionality.”
“E-mail, in its current state, is in dire need of a revisiting,” LeVasseur explains. “The existing design and architecture allows for virus attacks, ‘spam’ abuse and major security concerns.”
LeVasseur says the system he has created is versatile and includes multiple features. One of the main advances includes the secure transfer of e-mail messages through existing clients, without requiring a changed e-mail address.
In addition, e-mails can be completely tracked and users can view information about a message, including other recipients’ responses, before opting to open it. His patent application also includes private and public messages in a single communication, as well as a configurable cryptographic engine for storage.


