A VPN is a secure private connection between your laptop or Smartphone and the internet. It stands for Virtual Private Network and helps to hide your IP address from the websites you visit.
So, if you ever wanted to surf the internet anonymously or gain access to websites more privately, a VPN is the best way out. It works by encrypting all your traffic by use of an encryption tunnel.
Data from your laptop or computer first goes encrypted through a VPN server then on to the internet. BestVPN.com offers you some top VPN services in the market you might consider using.
Tor, on the other hand, is a browser designed to keep your online activity anonymous. It’s an acronym that stands for “the onion router”. Tor makes your browsing private by scattering your internet traffic across different several anonymous servers.
VPNs
The need to keep private has never been high. People want to keep their internet traffic private for reasons that are best known to them.
Some of the obvious reasons for online privacy include prying ISPs targeting your personal information, government surveillance, need to gain access to local restricted networks or fight internet restrictions imposed by oppressive regimes.
That said, open networks such as a public Wi-Fi connection are open to analysis and malicious attacks by cybercriminals. Some internet service providers (ISPs) also monitor your data to a certain degree.
You don’t want to lose your hard-earned cash because of entering your credit card details, passwords and usernames in some unsecured website. This is riskier if entering such information on websites using an open Wi-Fi network connection.
Most VPN developers have VPNs that use the 256-bit encryption. This is strong enough to keep you protected from government surveillance activities. Albeit, protective of your data, Virtual Private do not keep you 100% protected at most times.
They also come with their own security leaks. Unencrypted data such as IPs and DNS could get transmitted. As a VPN user, you also need to be wary of VPNs that keep logs. While many of these services promise not to retain the data of their clients, they fall short of keeping the end of their bargain.
Tor
Doubling up your online privacy with a Tor browser could be the next best course of action for you. Developed by the US. Navy in the 1990s, its primary purpose was to ensure safe online communications by intelligence agencies. The U.S government could use it to access foreign websites if it wanted to. Tor keeps their IP address a secret.
Later it was released to the public and its now licensed under a non-profit organization that researches and develops privacy tools for online use.
To put it basically, Tor an acronym for the onion router is software you install on your computer to enable the running of Tor. This software also enables you to manage Tor connections using a network of computers.
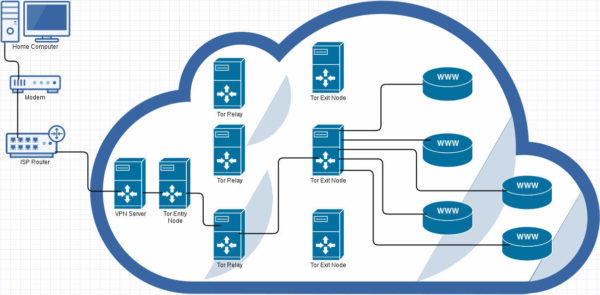
Termed as the tool for accessing the dark web, where most sites are not indexed by Google; Tor disguises its users on the internet by moving their traffic across multiple Tor servers. The data from your end appears to come from different Tor network nodes and not your computer. The nodes are the many computers found in a Tor network.
If many users are on the Tor network at one given time, your traffic is more protected. This many computers act like a layer that keeps you anonymous from other web users in the world. The computers in a Tor network responsible for the handing of intermediate traffic are referred to as Tor relays. These Tor relays are categorized into three different functional roles that include end relays, middle relays and bridges.
End relays enable the final relay of data in the wide Tor network while the middle handles traffic along the nodes in a Tor network. Ultimately, whether an activist or an average user the Tor network suits all as it guarantees you safety and privacy online.
VPN and Tor combined
Should I use a VPN service together with Tor?
I’m sure this is a common question in the minds of many VPN users.
After damning revelations about NSA, more people felt the need to protect themselves online. Snooping ISPs could easily reveal your personal information at their discretion.
If you are not using a VPN for your online safety and protection, then use a Tor browser. Without taking these precautions, you could fall victim to cybercriminals or face a lawsuit because of gaining access to government restricted websites.
Note, however, that a VPN use is necessary whether using a Tor browser or not. This is because not all this privacy tools are guaranteed to protect your privacy. Using them both means that each tool could cover for the security gaps brought about by the other.
How exactly should you combine a VPN with Tor?
There are two ways you want to use when using a VPN together with Tor.
First up, is the so-called ‘Tor over VPN’ This configuration works when you first connect to a VPN server then use the Tor browser. Using this sequence means your VPN server encrypts your use of the Tor browser. A VPN makes you an anonymous browser on the Tor network. Also, using a VPN hides your IP address from the Tor entry node as it relays an IP address your VPN provides and not your IP. On the downside, this method puts you at risk of getting exposed due to hacked Tor nodes.
The other method you want to know is a reverse of the first known as “VPN over Tor” To use this method, you first need to connect your computer to a VPN. This creates an encryption tunnel through which your traffic passes through to the Tor browser. After your data exits the node of a Tor network, it still moves encrypted to a VPN server and finally the internet.
With this method, your IP address is hidden from your VPN as it gets scattered over the Tor network. However, this method is quite difficult to configure.
The bottom line
All said, protecting your data online is paramount in this digital age. While online, you have the option of using a VPN or the Tor browser for browsing anonymously. Still, you have the option of using a combination of VPN and Tor. A VPN-Tor combination boils down to what combination suits your preferences best.