Update (20 October 2014): The Torsion project was renamed to Ricochet in June 2014. Since the article and the interview happened prior to renaming, this post references the project using its older name. It is advisable to substitute “torsion” with “ricochet” in commands listed in this post and wherever applicable.
Privacy on the Internet is something which is not very well respected by everyone. On one hand, big corporations like Microsoft, Google, Facebook and the like collect every detail of our online activity for serving targeted ads and other benefits. Also we have the NSA and other government agencies, who have been spying on people for a very long time. On the other hand, we are negligent about guarding our personal information and activities. Nevertheless, it is in our own hands how we deal with privacy, and we can stop being monitored by making right decisions and with the right choice of software. Using Off-the-Record encryption in instant messaging applications is one way to protect chats. Also, I had written about Telegram and a CLI client available for it in one of my last posts.
The day before yesterday, my friend Madhurya Kakati introduced me to a project on GitHub named Torsion. This project is really interesting, so I decided to write on it as I felt that everyone should be aware that it exists.
Say hello to Torsion!
Torsion is a peer-to-peer instant messaging app developed by John Brooks that aims to work without making you trust anyone with your identity, without sharing your contact lists and without leaking communications. Torsion claims that:
- You can chat without exposing your identity (or IP address) to anyone
- Nobody can discover who your contacts are or when you talk (metadata-free!)
- There are no servers to compromise or operators to intimidate for your information
- It’s cross-platform and easy for non-technical users
Torsion is a peer-to-peer instant messaging system based on Tor hidden services. Your login is your hidden service address, and contacts connect to you (not an intermediate server) through Tor. It is extremely hard for anyone to learn your identity from your address.
Torsion is a new experiment and its in a very early stage. The application is primitive and has not been audited or formally reviewed by anyone. But, nevertheless, it works nicely and is still a lot better at protecting privacy than a lot of other apps.
You can read about Torsion’s technical design here and in detail about the protocol here.
Getting Torsion
Getting a binary release
To use a pre-compiled binary of the app, you need to go to the releases page and download the latest binary release that is built for your OS. Windows users should use Torsion.exe and Mac users should use use Torsion.dmg. Its a portable executable that can run directly without installation.
Linux users should download the bzipped tarball, extract it and then run the Torsion binary inside it.
wget https://github.com/special/torsion/releases/download/v1.0.1/torsion-1.0.1-static.tar.bz2 tar -xvf torsion-1.0.1-static.tar.bz2 cd Torsion/ ./torsion
Done!
Compiling from source
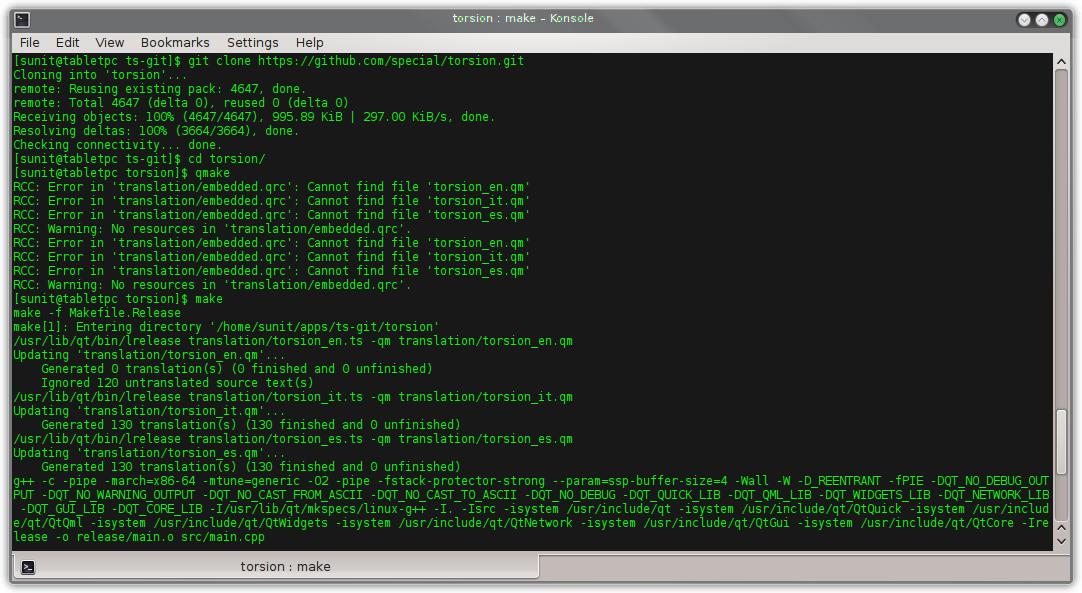
If you want the up-to-date version of Torsion with the newest commits then you should consider compiling from source.
Linux
Clone the git repository:
git clone https://github.com/special/torsion.git
Navigate to the directory:
cd torsion
Compile the application. Make sure you have the Qt SDK on your system.
qmake && make
Before we can launch the application, we need the tor binary to be placed in the directory of the application or in the PATH. You can either install Tor from the distribution repositories or you can grab the statically compiled binary from here and place it in the directory, making sure the file has executable permissions.
Then you can launch Torsion by:
./Torsion
If you wish to so a system installation instead of a portable one, compile with root privileges:
qmake DEFINES+=TORSION_NO_PORTABLE && make && make install
Then Torsion will be installed as a system application and will be available in the menu.
Windows
I haven’t compiled and tested the Windows version myself. So I quote the official documentation:
“Builds with MinGW or MSVC. You will need the Qt SDK and a copy of OpenSSL headers and libraries.
You must pass
OPENSSLDIR="C:\Path\To\OpenSSL\Build"
to qmake. If using Qt Creator, add it to Additional arguments in the Projects/Build Settings tab. The default build is portable and stores configuration in a
config
folder next to the binary. Pass
DEFINES+=TORSION_NO_PORTABLE
to qmake to use the user appdata location instead.”
Mac OSX
I do not have a Mac, so I again quote from the docs:
“Use the Qt SDK or homebrew. Run
qmake
and
make
to build an application bundle. The default build will store configuration in a
config.torsion
folder next to the application unless the path looks like a system-wide Applications folder, in which case
~/Library/Application Support/Torsion
is used.”
Using Torsion
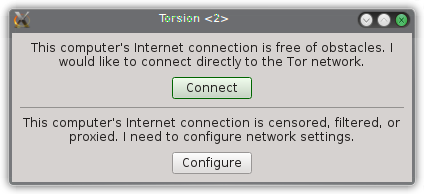
When Torsion is first launched, it shows up a window for configuring Tor to connect to the Internet.
If you have a direct connection, click “Connect”. If you are behind a proxy, click “Configure”.
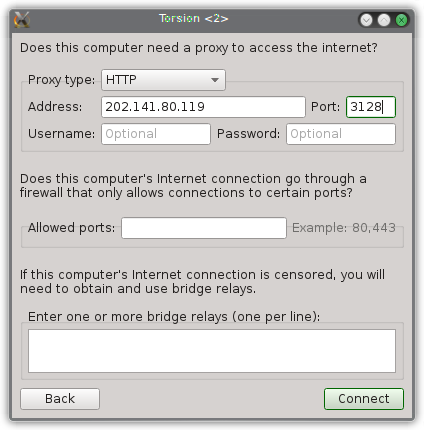
If you choose to “Configure”, you will be presented a window to fill out your details before hitting “Connect”.
The app doesn’t ask you to sign up to use it. Neither does it ask you for your personal details. All it does is generate a Torsion ID (like torsion:rs7ce36jsj24ogfw) for you to share with your friends so that they can contact you.
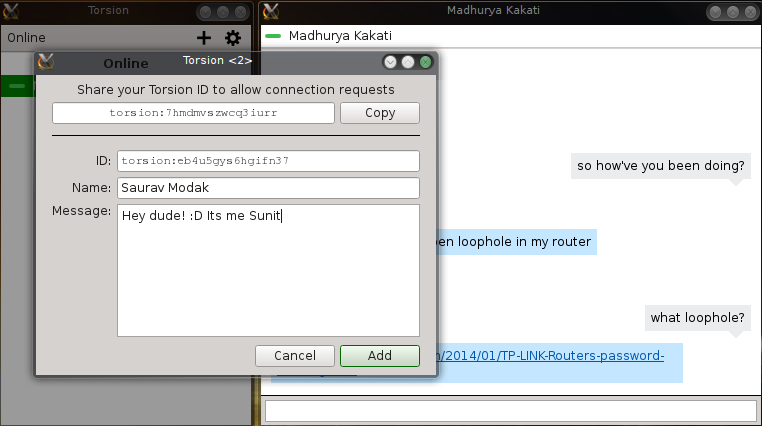
Once you are connected, you will see the contact list. You can add a new contact using the “+” button. You will see the following window to connect to your contact:
All you need to do is enter your friend’s Torsion ID and fill out the rest and click “Add”. Your add request will be sent to your friend.
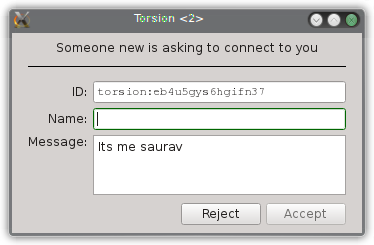
Conversely, if someone adds you, you get a request like this:
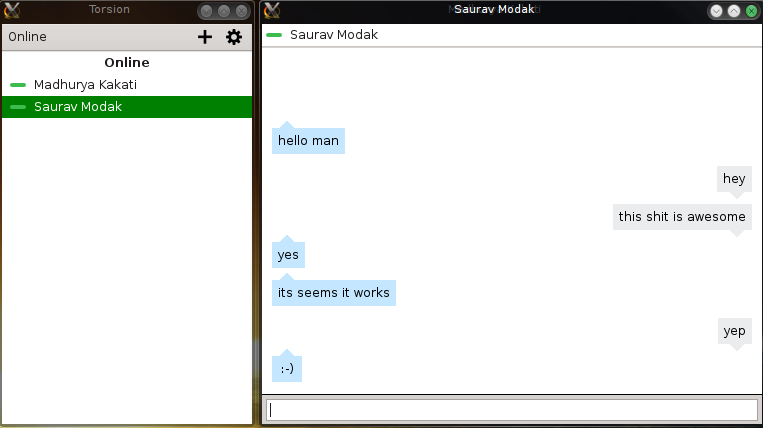
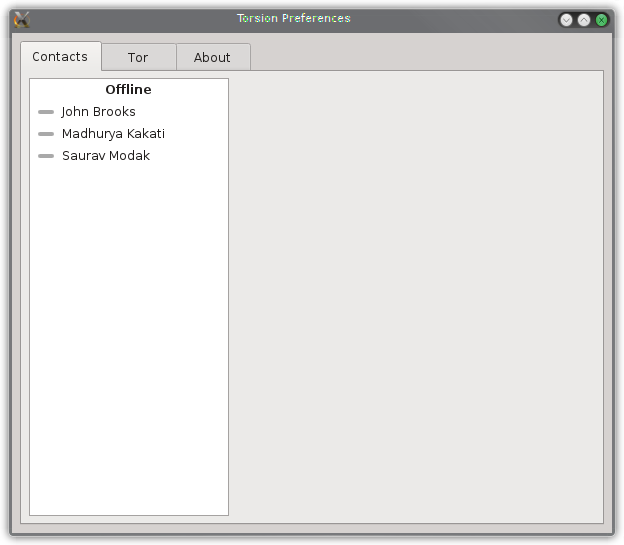
The contact list and chat window look like this:
The app doesn’t have support for notifications, smilies (emoticons), file transfer, etc. yet. However, all these features are likely to added in the upcoming releases as stated by the developer.
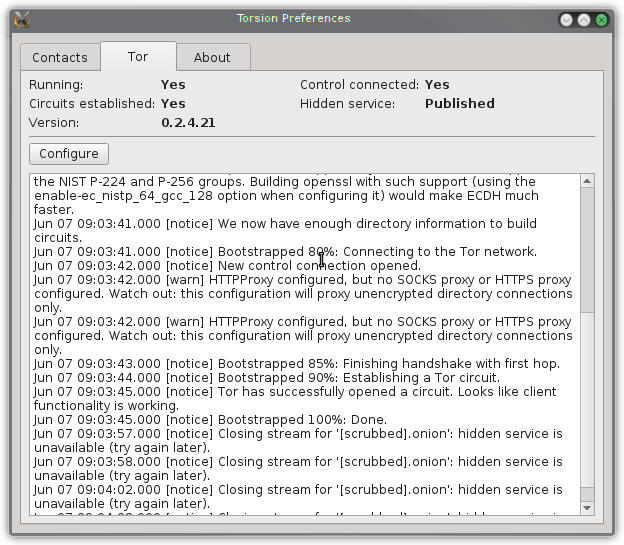
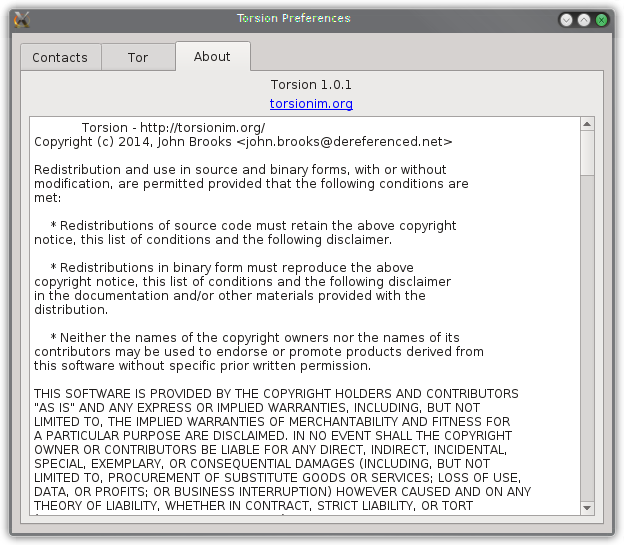
Clicking the gear button brings up the preferences window with three tabs, namely:
- Contacts, which shows details of all your contacts
- Tor, which allows you to configure Tor and read the Tor status logs
- About, which shows a big text box containing Torsion’s software license agreement
I thank Saurav Modak for helping me test drive the app and collect screenshots.
Moments with the developer
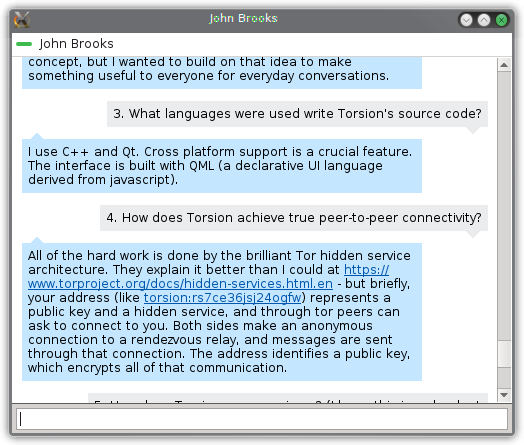
Being impressed with the app, I decided to talk to the developer John Brooks via Torsion (of course, duh!). He’s an extremely nice guy who answered all my queries regarding the app and we also had a casual chat regarding open source software.
He also agreed to an interview for our blog.
Here’s the conversation:
Sunit: Hello John! Your app is wonderful.
John: Hey! Thanks a lot. 🙂
Sunit: How would you describe yourself?
John: I’m a self-taught developer; I started writing software because I enjoy creating something useful and solving problems. I grew up and learned through OSS until it became a career. I follow my interests and passion wherever it goes.
Sunit: How did you come up with the idea of Torsion?
John: I’ve been interested in Tor for a long time. I use it often and I’ve studied it well. I wanted to build something in support of online anonymity, and this was a natural fit. The ideas were inspired by TorChat, which is very interesting as a proof of concept, but I wanted to build on that idea to make something useful to everyone for everyday conversations.
Sunit: What languages were used write Torsion’s source code?
John: I use C++ and Qt. Cross platform support is a crucial feature. The interface is built with QML (a declarative UI language derived from javascript).
Sunit: How does Torsion achieve true peer-to-peer connectivity?
John: All of the hard work is done by the brilliant Tor hidden service architecture. They explain it better than I could at https://www.torproject.org/docs/hidden-services.html.en – but briefly, your address (like torsion:rs7ce36jsj24ogfw) represents a public key and a hidden service, and through tor peers can ask to connect to you. Both sides make an anonymous connection to a rendezvous relay, and messages are sent through that connection. The address identifies a public key, which encrypts all of that communication.
Sunit: How does Torsion ensure privacy?
John: Most importantly, everything happens through Tor. There are no servers, no single point that can be intercepted. Connections are encrypted end-to-end, so no relay can see content, and no relay can identify both you and who you’re talking to. Your contact list and private key are stored only locally, and you can’t be impersonated without them. It’s a very complicated topic and there is always room to improve. I can say that Torsion does more than any other messenger to keep your identity, who you talk to, and what you talk about private.
Sunit: Does Torsion feature end-to-end encryption like OTR?
John: The connections are always encrypted with the public key of your contacts, and they have forward secrecy as well. Right now, this is just the standard encryption that is used for all hidden services; it’s sufficient, but it’s not the same as something like OTR. OTR itself isn’t very useful in this architecture, but adding other layers of cryptography – a defense in depth – is an open question to research.
Sunit: How do you think Torsion is different from/better than other private messengers?
John: There are a lot of new messaging tools focused on protecting the content of your conversations – and that’s great. But what they can’t protect is metadata; they have servers that can see your contact list, how often and when you talk to specific people, and where you’re connecting from. We’ve seen proof recently of how valuable that information can be. Those servers – or governments that could intimidate them – can even block and disrupt your conversations. Those are problems you can’t solve in the traditional internet, so nobody else is trying. The anonymity from Tor and the freedom with peer-to-peer connections gives Torsion a unique position to fix that.
Sunit: What new features/changes can we expect in the upcoming releases? Where do you expect to see Torsion in the future?
John: My next goal is quality, to become as seamless and easy-to-use as any standard messaging software. We’ll see what becomes important as the project grows, but I have been working on designing more advanced architecture on top of hidden services and useful additions like file transfer. I would like it to be something that any privacy-aware person can use every day, and something that the paranoid can rely on to protect themselves and their identity.
Sunit: The desktop release is wonderful. Are you planning to release a version for mobiles (iOS and Android)?
John: It’s absolutely possible, but there are some unique challenges in bringing this system to mobile. I’ll be focused on the desktop, but contributions would be very welcome.
Sunit: What are the other projects you’re involved in?
John: Recently, this is my only personal project, but I also work on Sailfish, a Linux-based mobile OS, and the many opensource projects underneath it
Sunit: What would you say to our readers and Techno FAQ community members regarding open-source software, freedom, internet privacy and the like?
John: There is nothing more important to a society than unrestricted, unmonitored communication – there is no freedom without it. Personal privacy is just as important to personal communication. The internet is the greatest tool in history to build free society and enable sharing. We must innovate in open, pro-privacy tools faster and better than the people who would undermine them. You should support Tor, the EFF, and everyone trying to build a better internet.
Sunit: Thanks a lot for your precious time and patience for answering my queries. We’re grateful to have people like you in the OSS world who contribute a lot to the cause of internet privacy.
John: Thank you! This is a project of passion, eating up my spare time, and it’s very motivating to have people take interest. I hope to take it much further and build an essential tool for people to rely on. I’m always happy to discuss these problems and how opensource software can change the world.
Conclusion
Torsion is a very promising IM app that aims to change people’s attitude towards private messengers. It is much quicker to set up and easier to use than, say, OTR or Telegram. Neither does it require you to register or have an IM account anywhere nor does it ask you for your personal information. Your generated Torsion ID is sufficient for people to identify and connect to you. At the same time, it tries to maintain privacy by encrypting chat traffic and routing it through Tor. More features will also be added with time, so it is an interesting project to keep an eye on.
If you are looking for an easy-to-use, no-frills private messenger, you should definitely give it a go. If you are a developer, you can contribute to the project on GitHub by forking it, adding new features to it and merging it back, thus improving the usability of the app.
In this era of internet censorship, monitoring, logging and data mining by big corporations and governments, an app like this is a welcome change, a change towards freedom and towards safeguarding our basic human rights.


5 Comments
Bibhuranjan
7 June, 2014I think this should be out on mobiles as well. A majority of the population have moved to mobiles for daily communication. Many even don’t use desktops to chat at all. So please a mobile version request Mr. Developer.
🙂
Sunit Nandi
7 June, 2014The developer has stated that if he recieves enough contributions and support from other people, we might have a mobile version one day.
netsurfer912
7 June, 2014An Android port should be very simple since he uses Qt …
Sunit Nandi
7 June, 2014Maybe I try porting it once I have enough time in my hands.
Madhurya Kakati
7 June, 2014The interview with the dev is a nice addition. Nice article.