Cybersecurity-as-a-service: Your Business Needs It!
Let’s start with some positivity! Businesses can save up to $1.4 million per attack by deploying cybersecurity-as-a-service and 73% of major organizations attribute cybersecurity to their success. (Source)
But why is cybersecurity such a big deal?
According to the same report, businesses lost over $3.5 billion in 2019 due to cyber-attacks and it is expected to multiply up to 10 times in the next 5 years.
Thus, making it one of the biggest threats to the business world.
What Exactly Is Cybersecurity-as-a-service (CSaaS)?
Cybersecurity is a risky prospect. So outsourcing it directly brings a set of challenges. And cybersecurity-as-a-service solves this issue with a unique approach.
Cybersecurity-as-a-service is a unique model of cybersecurity management where only a few features i.e. the services that need streamlined focus are outsourced and others are monitored in-house.
This innovative approach delivers balanced performance by dividing the tasks between your in-house team and the outsourced CSaaS.
How Will Cybersecurity-as-a-service(CSaaS) Help Your Business?
Cyber security is not a one-step solution. This multi-level solution comprises a dedicated layer for each problem. These layers are specifically designed to tackle a single threat.
Example: If you have a dedicated framework designed for security monitoring and it encounters a threat, then the layer that detects the threat will inform all other layers of the potential problem and tackle it on an individual level. If the threat bypasses that layer, then in the next stage the firewalls will protect the system. If the threat bypasses that too, the alert system notifies the system administrator, and so on…
These layers consider every possible scenario to protect your business. Moreover, with the arrival of new technologies like 5G, next-generation cyber threats may start to haunt your company with even more advanced and innovative attacks. Thus, leveraging cybersecurity service for your business is the best way to move forward without worrying about all these security complications.
Here’s a detailed guide on how the cybersecurity framework will do that:
a. Endpoint Framework
This framework follows a 6-step protection plan:
Contain :- Isolate :- Deny :- Reduce :- Permit :- Demote
- Contain- denies action from high-risk applications and utilities.
- Isolate- alters resources
- Deny- restricts untrustworthy scripts
- Reduce- limits exposure
- Permit- makes the right decision
- Demote- makes the processes harmless
This may seem too technical. So, here are some real-life use cases:
This 6-step protection plan will prevent your system from non-malware attacks, code injection attacks, remote code execution attacks, unpatched app attacks, ticket attacks, and other malicious attacks.
Non-malware attacks: Also known as fileless attacks, this is the newest type of cyber attack where an attacker corrupts the Windows file and turns it against the system. A non-malware attack doesn’t make use of external files.
Code injection attacks: Also known as Remote Code Execution (RCE) attacks, it exploits the language aspects of software instead of making use of a command.
Unpatched application attack: A software is not always perfect. Hence, to make it work better, developers push software patches, which are essentially fixes for the loopholes. Attackers take advantage of this situation and exploit a system before the patch has been pushed.
Here’s How Endpoint Framework Works:
This framework detects, responds, and nullifies a threat in a systematic manner. And all this is made possible with the help of an SGN – Secure Global Network.
An SGN makes it possible for an organization to communicate from multiple places with absolute security and encryption.
Layers of SGN Infrastructure:
Network Security
Network security acts as the first layer of security. It takes care of all the essential security measures to keep the threat at bay. Features like firewall and encryption will make sure that your internal communication cannot be deciphered and the network remains intact.
The anonymous IP (Internet Protocol) will keep your web address secure and leave the attacker clueless.
Types of network security:
- Cloud VPN (SGN)
- ZeroTrust (SGN)
- Firewall or DPI
- Encryption system
- IDS/IPS
- Anonymous Public IP
- Secure DNS
Incident Response
This layer of security will make use of AI (artificial intelligence) to notify the system administrator of any potential threats. The AI analyzes the data and determines the threat level.
Types of incident responses:
- AI alert system
- Integrated SIEM
- Quarantine capability for devices
Governance, Regulatory, & Compliance
This layer scans the network periodically to filter out all the loopholes and strengthen the system.
Types of governance, regulatory & compliance:
- Threat Intelligence
- Policy Mapping
- Threat analysis
b. Endpoint Protection With AI
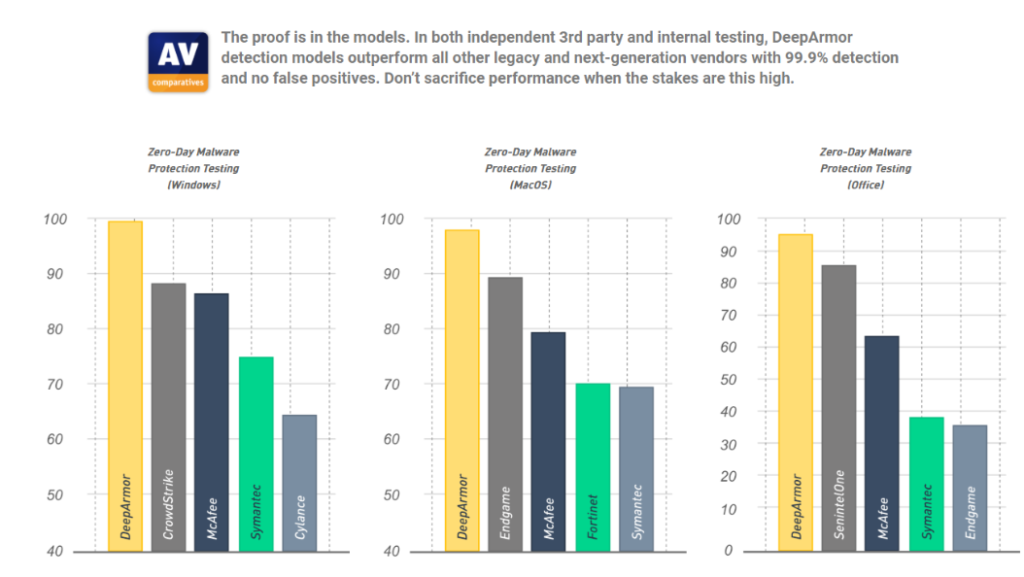
(Image Source: Xperteks)
DeepArmour, McAfee, and CrowdStrike are three major players in the endpoint protection market. We, at Xperteks, use the best that the industry has to offer.
For cybersecurity-as-a-service, we use DeepArmour’s next-generation AI-driven endpoint protection.
This endpoint protection system along with making use of AI, incorporates big data and machine learning capabilities. This eventually predicts future attacks like phishing and prepares the system to tackle threats more efficiently.
These phishing attacks can be triggered through PDFs, documents, or even some application files. Thus, analyzing these modern attacks and making use of AI and big data is the only way forward.
Other Best Practices
‘Cybersecurity-as-a-service’ safeguards the software aspect of your business. Hence, if the physical security gets compromised even the software aspect of your business could be exploited. Thus, choose a cybersecurity service that can handle your entire business infrastructure without any hiccup.
The ideal cyber security solutions for government should consist of:
- Physical Security
- Managed Detection & Response
- Cybersecurity-as-a-service
With these 3 solutions at your fingertips, you can expect your business to reach new heights without any hindrances.
(Image Source – Markus Spiske on Unsplash)